18 Mar 2024
Welcome to the Threat Context Monthly blog series where we provide a comprehensive roundup of the most relevant cybersecurity news,...
13 Mar 2024
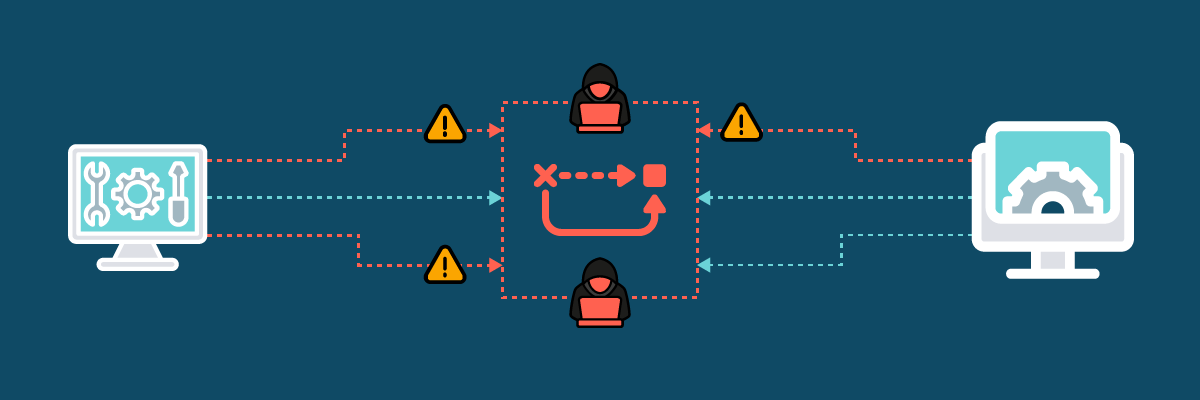
There are IT security shortcuts that might be well-intentioned and seem sensible at the time, that could have serious and...
04 Mar 2024
During a recent customer assessment, our pen testers discovered a critical vulnerability that exemplifies the importance of manual and continuous...
01 Mar 2024
A recent advisory issued by the Cybersecurity and Infrastructure Security Agency (CISA) has shed light on vulnerabilities in Ivanti VPNs...
19 Feb 2024
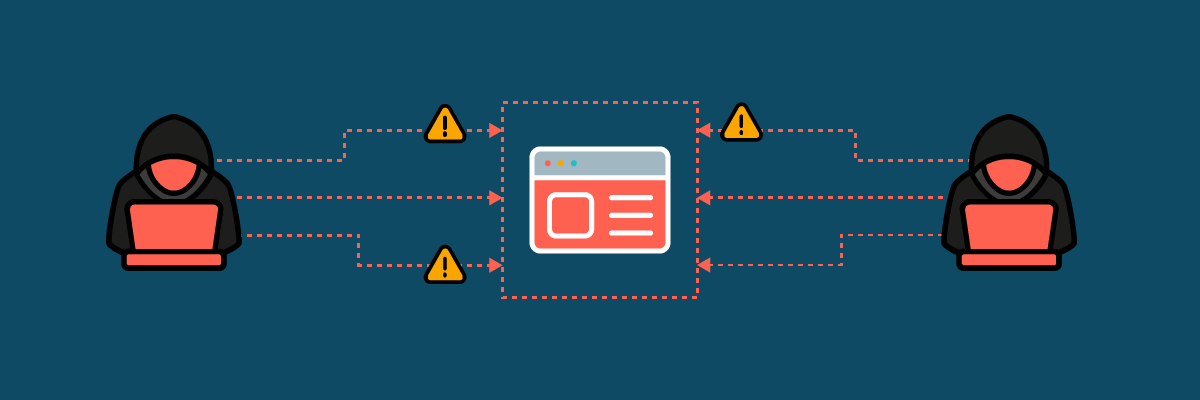
Web applications are an integral part of our daily lives, used for everything from banking and shopping to social networking...