
Proactive Cybersecurity Strategy: Reducing Risk Ahead of Time
A proactive cybersecurity strategy is no longer optional. Learn why and how you can implement proactive security in your organization.
Read moreContinuously discover and monitor unknown internet-facing assets, prioritize risk with AI-driven insights, and monitor your attack surface to reduce exposure before attackers exploit it.
Get a clear, continuously updated view of your external attack surface. Outpost24 EASM helps security teams identify exposures faster and focus remediation where it matters most.
Outpost24 EASM provides a complete and continuously updated view of your internet-facing assets, helping security teams identify unknown exposures, prioritize risk, and reduce their external attack surface with confidence.
Automatically discover and inventory all internet-facing assets using passive, hybrid, and advanced reconnaissance techniques. Build a complete and continuously updated asset register covering domains, IP addresses, cloud infrastructure, and shadow IT — without requiring agents, credentials, or network access.
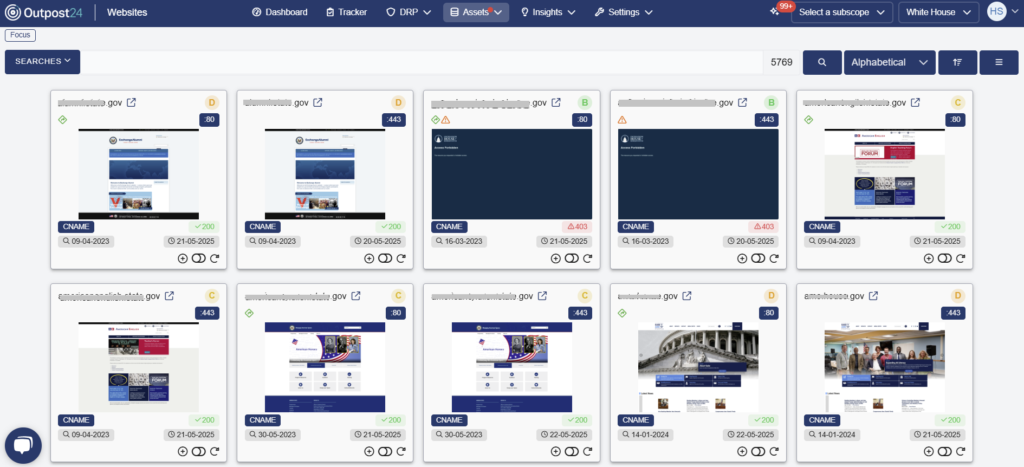
Continuously monitor your external attack surface to detect newly exposed assets, configuration changes, and emerging risks as they occur. Real-time alerts enable security teams to respond quickly and maintain an accurate, up-to-date view of their organization’s external exposure.

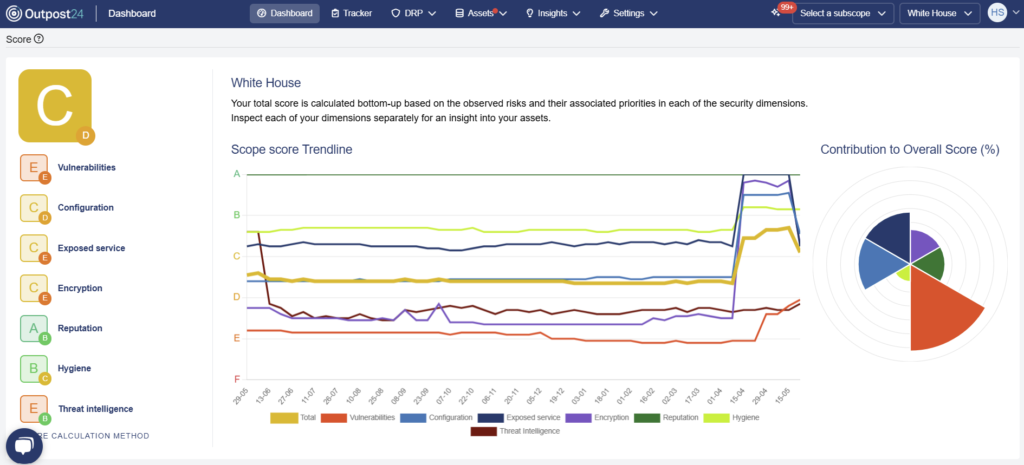
Understand which exposures pose the greatest risk with automated attack surface scoring and contextual analysis. Assets and findings are assessed and prioritized based on exposure and impact, helping teams focus remediation efforts where they will reduce risk most effectively.
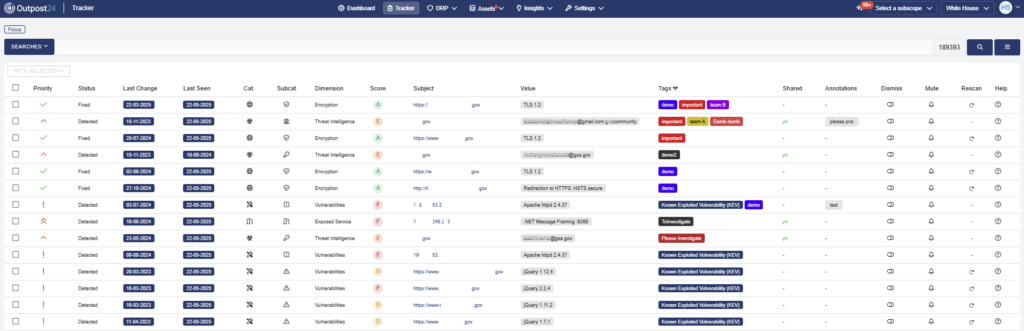
Manage remediation efficiently with interactive dashboards, prioritized trackers, and clear visualization of your attack surface. Monitor risk trends, track remediation progress, and give security teams the visibility and structure needed to reduce exposure over time.

Outpost24 was the only European Cyber Security Company named an Overall Leader in KuppingerCole’s 2025 ASM Leadership Compass.
We were also recognized as a leader in both the Product and Market categories by KuppingerCole, leading analysts in the areas of digital identities, authentication, and cybersecurity.

Simplify your compliance and audit efforts. Outpost24 EASM is designed to align with these common regulatory and industry requirements:

Expert Help, When You Need It
Extend your team with Outpost24 security experts who continuously monitor your attack surface, investigate exposures, and provide prioritized guidance to help you reduce risk faster.
An EASM solution offers continuous discovery, analysis, and monitoring of everything connected to your company’s online exposure, including domains, websites, hosts, services, technologies, SSL certificates, and more.
Through real-time discovery, an EASM platform keeps you informed of any changes or issues that may arise in the external attack surface of your organization. With this comprehensive solution at your disposal, you can have peace of mind knowing that your online assets are secure, and your company’s reputation is protected.
With Outpost24’s EASM platform, you can easily gain situational awareness of all changes in your online attack surface. This means you will be the first to learn about any vulnerability or issue that may encourage cybercriminals.
Our automated solution also enables you to reduce the risk of a cyberattack by identifying and analyzing vulnerable assets in real time, even those you don’t know about. Additionally, our EASM solution continuously scans and prioritizes findings on what to address first through quantitative risk ratings. As a result, it saves valuable time and frees up resources to focus on other tasks.
We offer a quick and effortless onboarding process that eliminates the need for any software or agent installation. The platform is cloud-based and easily accessible through a secure login via your internet browser. Our zero-knowledge approach only requires basic information such as the company name or primary domain to get started.
The platform suggests new primary domain candidates and allows for the importing of additional IP addresses, ensuring that the scope remains complete and up-to-date.
Sweepatic is a cybersecurity company founded in 2016 in Leuven (Belgium) specializing in External Attack Surface Management (EASM). Its EASM platform helpes organizations discover and monitor their internet-facing assets to reduce exposure to external threats.
In 2023, Sweepatic was acquired by Outpost24, a Swedish cybersecurity company, to enhance its capabilities in external threat detection and expand its security portfolio. The integration of Sweepatic’s technology into Outpost24’s EASM platform enabled a more comprehensive solution for continuous asset discovery, risk analysis, and attack surface management (ASM).
Explore additional resources.


Please fill in your information to submit a demo request. All fields are mandatory.
We’ll map your current situation and show you first-hand how Outpost24 EASM can immediately start boosting your cyber resilience.
Check our latest research, blogs, and best practices to level-up your cybersecurity program.

A proactive cybersecurity strategy is no longer optional. Learn why and how you can implement proactive security in your organization.
Read more


Understand the importance of CMDB accuracy in cybersecurity, and how security teams can ensure their CMDB can remain up-to-date.
Read more


Learn how a more integrated cybersecurity environment can enable stronger defense with advice from Outpost24 experts.
Read more