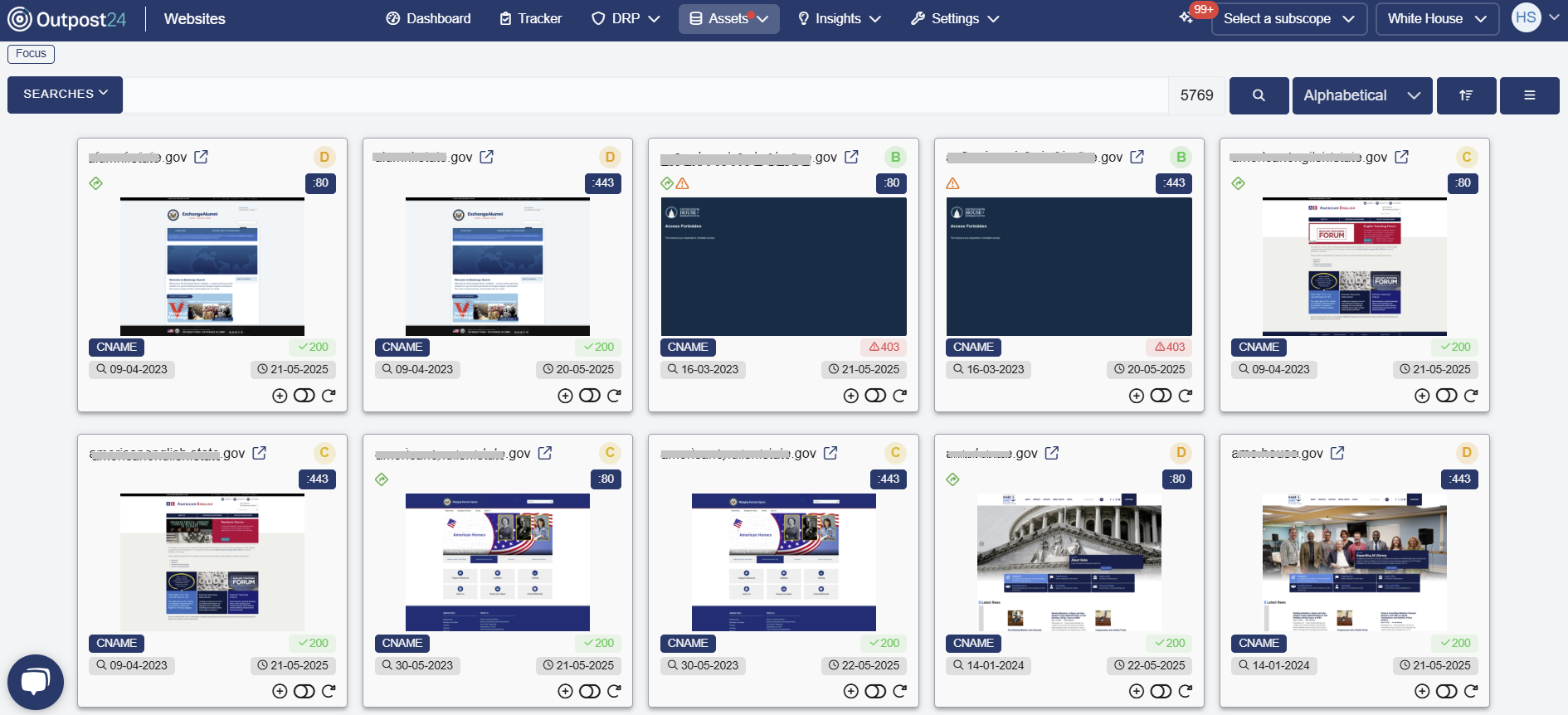
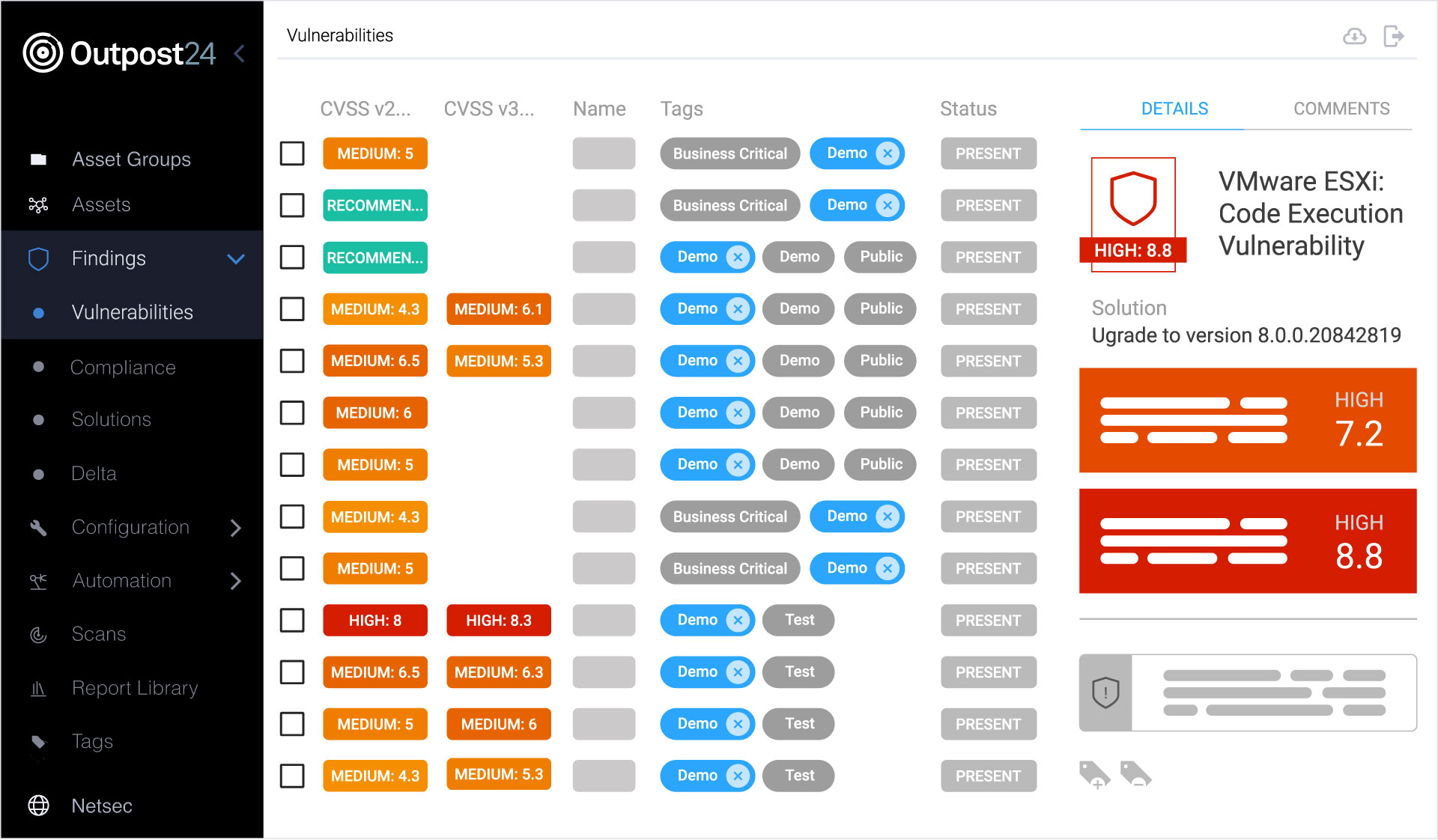
Products
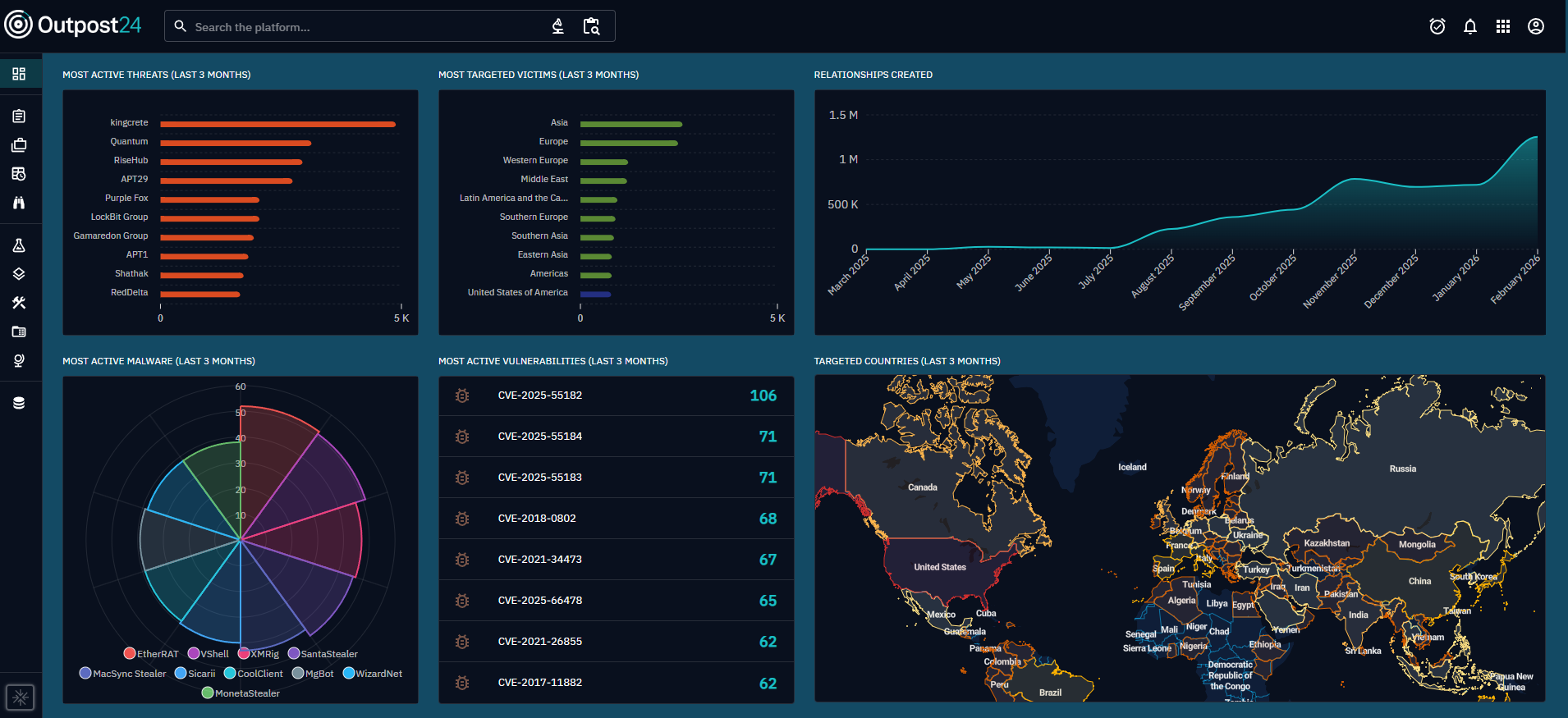
Outpost24 Cyber Risk Management Products
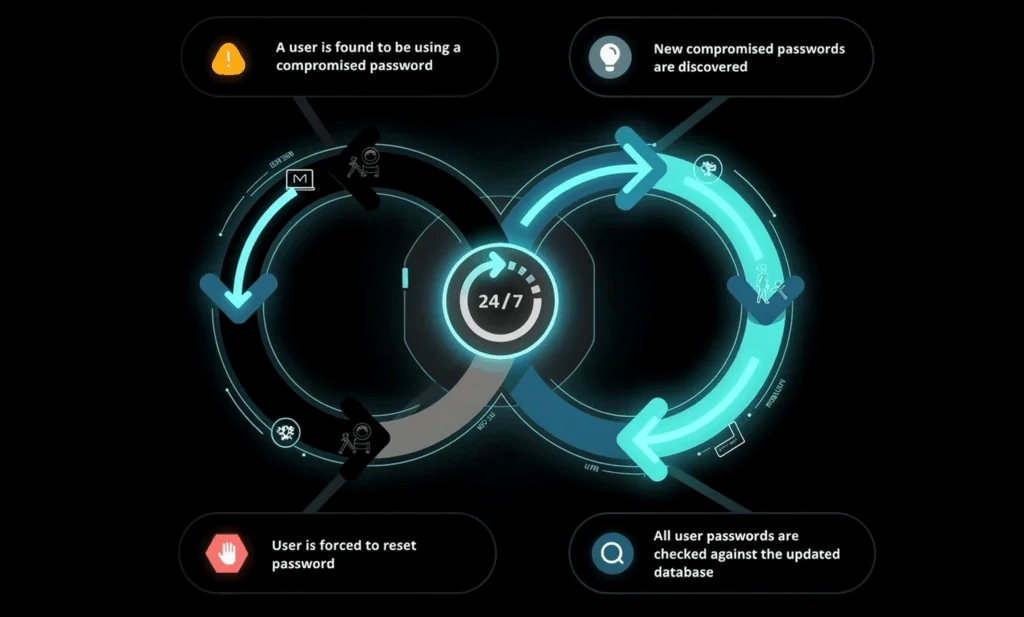
Our products offer continuous visibility across your entire attack surface with clear, actionable context for faster defense against threat actors targeting your organization.
Our Products
We elevate security teams with intelligence-led cyber risk management solutions.