Ransomware Report 2023: targets, motives, and trends
Our annual Ransomware Report shares the latest trends and developments of the most active threat groups to help businesses better protect themselves
Introduction
The prevalence of ransomware attacks reached unprecedented levels in 2022. After closely monitoring the most active ransomware groups in the last year, the KrakenLabs research team at Outpost24 is sharing the identified trends, and victim profiles of the targeted businesses, while exploring some potential motives behind the attacks. As ransomware continues to evolve, it is important for individuals and organizations to be aware of the latest trends and developments in their tactics, techniques and procedures (TTPs) to protect themselves from these threats.
Many ransomware gangs follow the double-extortion model, disclosing the names of their victims as well as the stolen data in their own Data Leak Site (DLS). By closely monitoring the most active ransomware groups that have their own DLS, we can detect, almost in real-time, the publication of attacks on different companies by ransomware groups.
Despite the disappearance of prominent threat groups such as CONTI and the old REvil, existing entities like LockBit, BlackCat, Hive, and Karakurt have demonstrated exponential growth and the number of victims surpassed previous records. There is also the emergence of new groups, such as BianLian or Black Basta, demonstrating a level of impact that rivals or even surpasses that of more established groups. To learn more about RaaS groups and how they operate, please refer to our past blog post: Ransomware as a Service: Behind the Scenes.
Ransomware activity in numbers
The researchers at Outpost24 detected a total of 2363 disclosed victims (businesses) by various ransomware groups on DLSs in 2022.
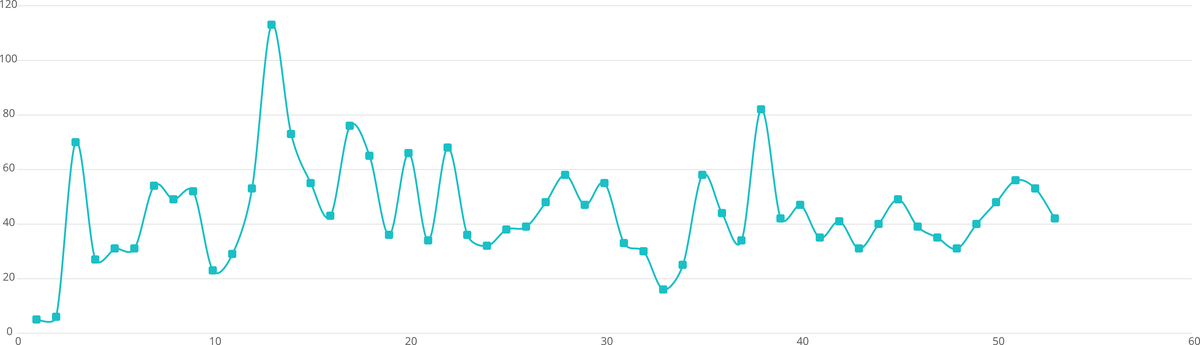
Plotting a graph of the attacks spread over time by week, we notice some patterns and oddities. For example, in the 13th week of the year (March 21), we detected more victims than usual. One could quickly think of a correlation between this spike in victims and the initiation of operations by Russia against Ukraine. However, a more profound analysis of the data performed by Outpost24 analysts shows that correlation does not necessarily imply causation. If we look through the victims, we see that only two attacks were committed against Russian companies, one perpetrated by the group known as BlackCat in March and another by the Cuba group in June. Furthermore, we have not identified any instances of financially motivated ransomware attacks against Ukrainian entities within the data leak sites. Both ideas fit with the fact that most cyber-attacks between Russia and Ukraine have not been ransomware ones but primarily in the form of data wiping and denial of service attacks, as reported by the Cybersecurity and Infrastructure Security Agency (CISA) and other agencies.
Another interesting pattern that can be correlated with an event was during week 35 and the following weeks. During that time, LockBit group claimed that they were being attacked as a consequence of leaking some of Entrust’s data, a cybersecurity company that was attacked previously by them. During that time, Outpost24 KrakenLabs detected that not just LockBit, but many other ransomware DLSs were under a DDOS (distributed denial of service) attack. The following graph shows the availability over time for those sites that suffered the attack.
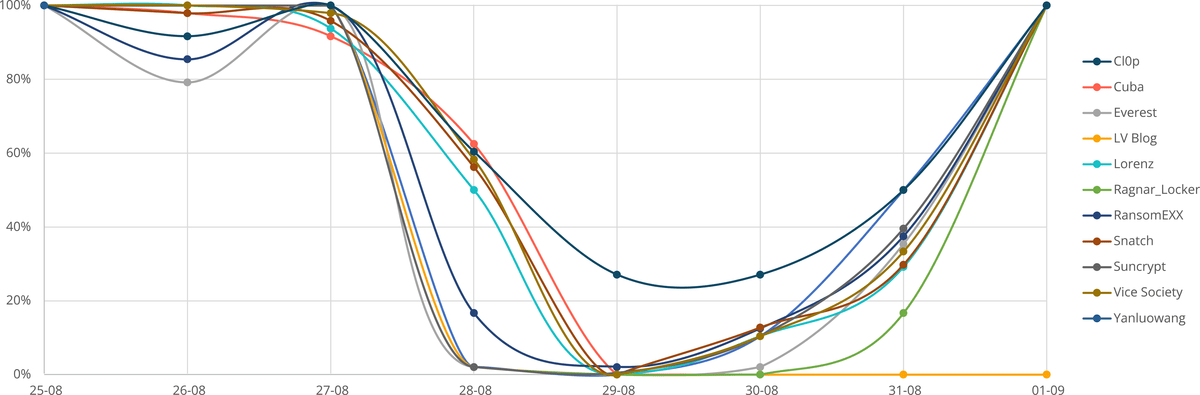
The fact that all of them follow the same pattern led KrakenLabs to believe, that a coordinated attack against them occurred during those dates. After they recovered normal availability, there was an increase in disclosed victims. That was an expected outcome since disrupting the availability of their DLS did not affect the affiliates’ operations, so in the end, the attacks just delayed the publication of the victims.
Most active ransomware groups in 2022
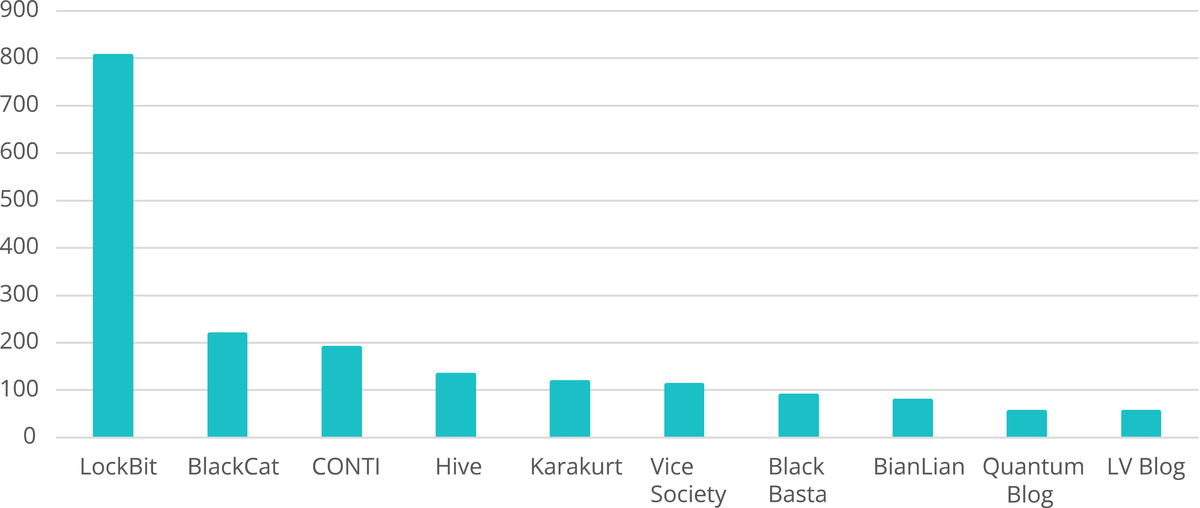
In 2022, the ransomware group known as LockBit exhibited a significantly higher level of activity compared to other groups.
Specifically, they were responsible for 34% of all recorded attacks during that year, averaging approximately 67 attacks per month; a total of just over 800 attacks. This is nearly four times the number of attacks attributed to BlackCat, the second most active group, with 215 victims disclosed.
The group’s activity during the year can be seen below:
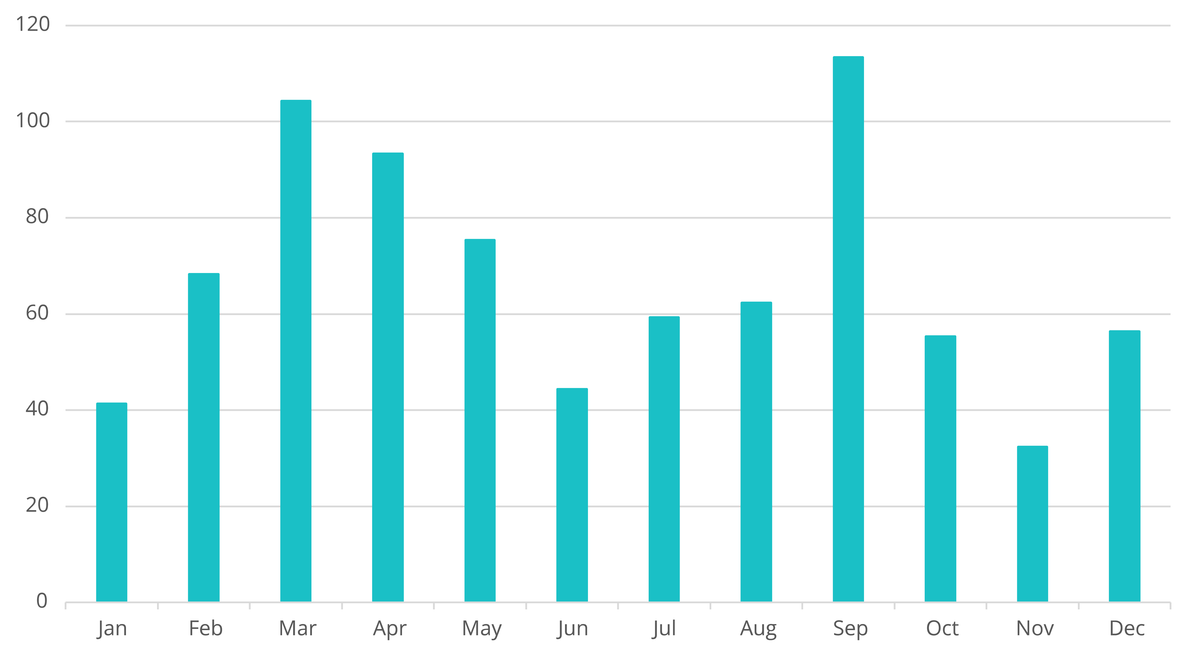
LockBit has been evolving throughout the year, becoming the most established Ransomware-as-a-Service (RaaS) organization by far. During June, one of their lesser activity periods, they revealed a new DLS named “Lockbit3.0”, altogether with announcing that they were using a new version of their malware, also “Lockbit3.0”. Later it was discovered that the new LockBit variant borrowed code from BlackMatter.
Coincidentally, their most active period was also an interesting one. In September, two of the malware’s builders were leaked by an alleged unpaid programmer of the team.
In November, a man was arrested in Canada for participating in LockBit’s criminal campaigns. This fact would explain the dip in activity during that period, as some affiliates might have considered laying down for a while.
Short-lived ransomware groups
During the year we have seen many new groups entering the ransomware scene, only to cease their activity shortly after. Entropy, Sparta and Stormous, to name a few. Some of those groups, like 0mega, have been keeping an extremely low profile, waiting for months between attacks.
Short-lived ransomware groups are cybercriminal organizations that carry out a few ransomware attacks and then disappear. Most of these groups are motivated by a desire for quick financial gain, as they can make a hefty sum of money from a single successful attack. Usually focusing on small targets, these groups typically demand lower ransoms, not only facilitating getting paid but also reducing the mediatic impact of their attacks and in turn, the attention they get. This methodology also helps them to evade detection and prosecution.
Additionally, some short-lived ransomware groups may be motivated by a desire to cause disruption or to target a specific organization or individual.
Conversely, certain short-lived ransomware groups might be related to larger operations in which more threat actor groups were involved, and the ransomware attack was just another stage of a longer operation. However, the underlying motivation of this type of group is usually unknown. But when a quick buck is not enough, some groups opt for the rebranding strategy. This helps them continue with a low profile and very few attributions while also maintaining their operations alive. For example, it is known that Onyx rebranded into Vsop around mid-November 2022.
Ransomware victim analysis
Based on the data collected, Outpost24 KrakenLabs analysts were able to understand what these groups are after and give a clear picture of the status quo of RaaS.
Insights on the sector
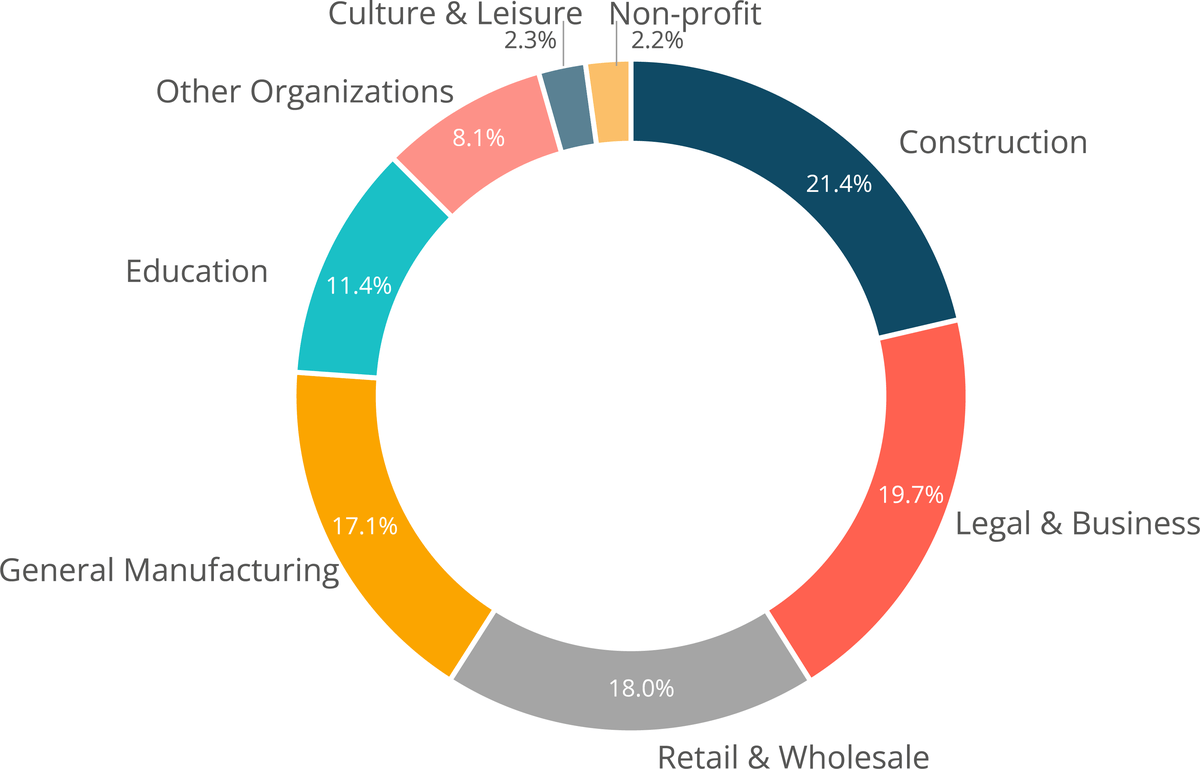
Regarding the most affected sectors, commercial and business-related companies were the most affected by ransomware attacks. As the following graphic shows, Commercial Facilities, Financial, Construction, Legal & Business and Retail & Wholesale sectors were the most affected, suggesting with medium confidence that threat actors are primarily targeting organizations that may have a higher capacity to pay a ransom. This highlights their financial motivations, as they seem to be following the tactic of Big Game Hunting (BGH).

Sectors that tend to have more valuable assets and a larger customer base are seen as more attractive targets by the attackers. Such is the case with the Financial or the Commercial Facilities sectors.
The companies within these sectors also tend to have more employees and third-party vendors, increasing the number of potential attack vectors. Securing all access points from companies with many employees and contractors working in distinct locations is inherently harder.
In other cases, when maintaining the confidentiality of their clients’ data is critical for the organization, victims may be more inclined to pay the ransom. Such is the case for the Legal & Business sector.
In any case, it is important for these organizations to be particularly vigilant in protecting themselves against ransomware attacks by implementing robust security measures and training employees to recognize and report suspicious activity.
KrakenLabs analysts noticed several cases where the same company was attacked multiple times by the same or even different ransomware groups. For example, in May CONTI and Hive disclosed the same victim the same exact day. This could imply that initial access brokers profit from selling a company’s access multiple times to different buyers.
Some other causes of multi-attacks on companies could be:
- Failure to learn from previous attacks: If a company does not thoroughly analyze and learn from previous attacks, they may be more likely to fall victim to similar attacks in the future
- Payment of ransom: Some companies may choose to pay the ransom demanded by the attackers in order to regain access to their data. This can encourage future attacks, as attackers see that they can be successful in extorting money from the company.
- Lack of segregation in the network: Failure to segregate the network and not having a proper segmentation of the network, making it easy for the attackers to move laterally and infect other parts of the network in further attacks.
- Attractive target: Some companies may be targeted multiple times due to the sensitive nature of their data, the large amount of data they have, or their perceived ability to pay a ransom.
During 2022, many companies and organizations categorized as Critical Infrastructure Sectors (as defined by CISA) have been compromised by ransomware attacks.
Moreover, since the start of the Russo-Ukrainian War, it has been hypothesized that Critical Infrastructure Sectors were going to become a major target by threat actors.
However, Critical Infrastructure Sectors accounted for just over half of the attacks perpetrated (51%), with the other half of the attacks being non-critical sectors (49%).
One of the reasons why ransomware is particularly dangerous in critical infrastructure sectors is that these industries are more likely to pay the ransom in order to regain access to their systems and data. This not only perpetuates the cycle of ransomware attacks but also encourages the continued development and distribution of ransomware by cybercriminals.
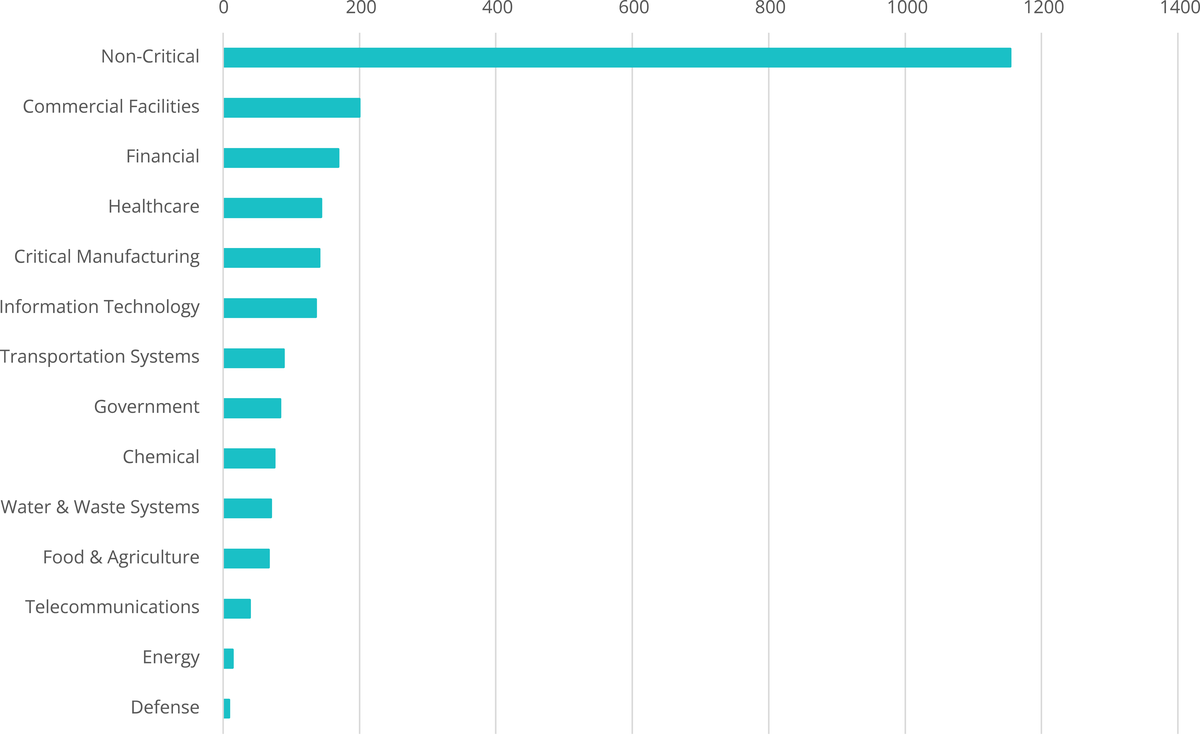
It is important to note that while most ransomware attacks do not target specific sectors, the nature of these attacks, which are often motivated by financial gain, may change over time.
Nevertheless, there are some groups that, for seemingly ethical reasons, choose not to attack certain sectors, such as healthcare.
On the other hand, some groups may also specifically target certain sectors.
A clear example is Vice Society and its focus on the education sector, specifically K-12 schools, which presents a lucrative opportunity for cyber attackers due to the presence of numerous potential attack vectors. This is most likely due to the lack of investment in cybersecurity measures and expertise among IT personnel within these institutions.
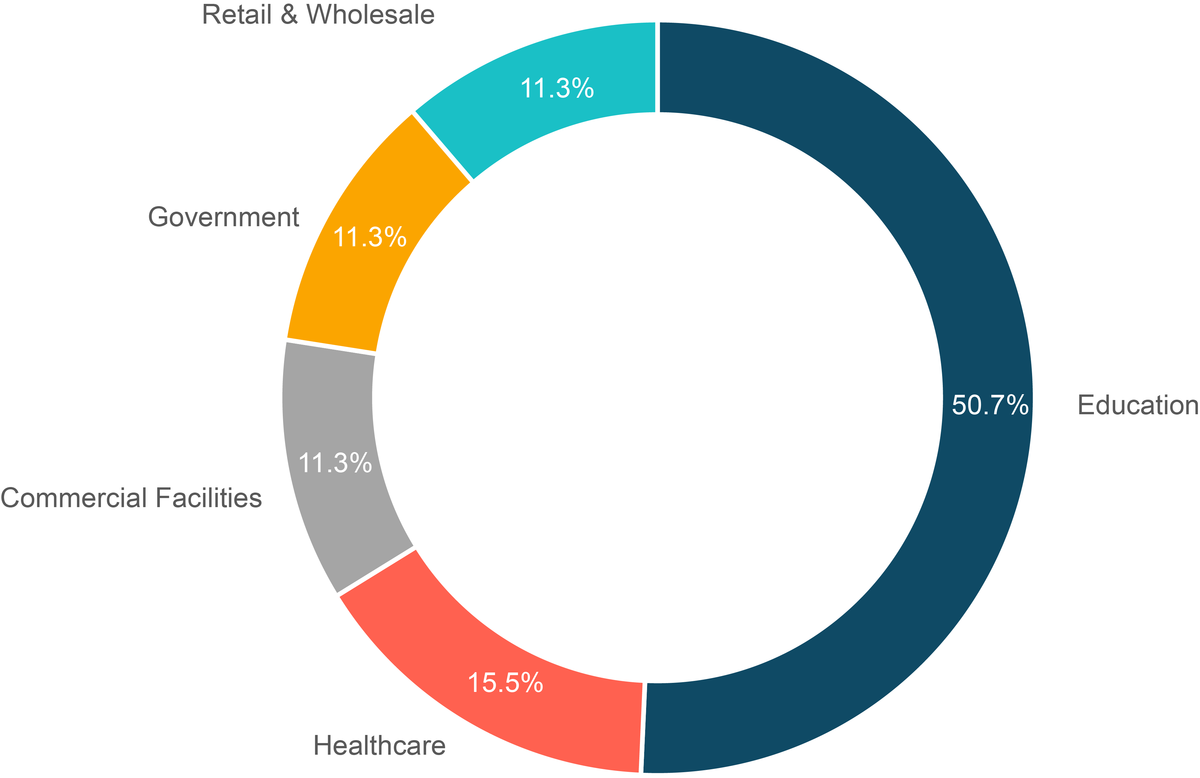
The FBI (Federal Bureau of Investigation), CISA, and the MS-ISAC warned about Vice Society and the threat it poses to education sectors in a joint Cybersecurity Advisory (CSA):
“Over the past several years, the education sector, especially kindergarten through twelfth grade (K-12) institutions, have been a frequent target of ransomware attacks. Impacts from these attacks have ranged from restricted access to networks and data, delayed exams, canceled school days, and unauthorized access to and theft of personal information regarding students and staff.”
Geographical distribution of the victims
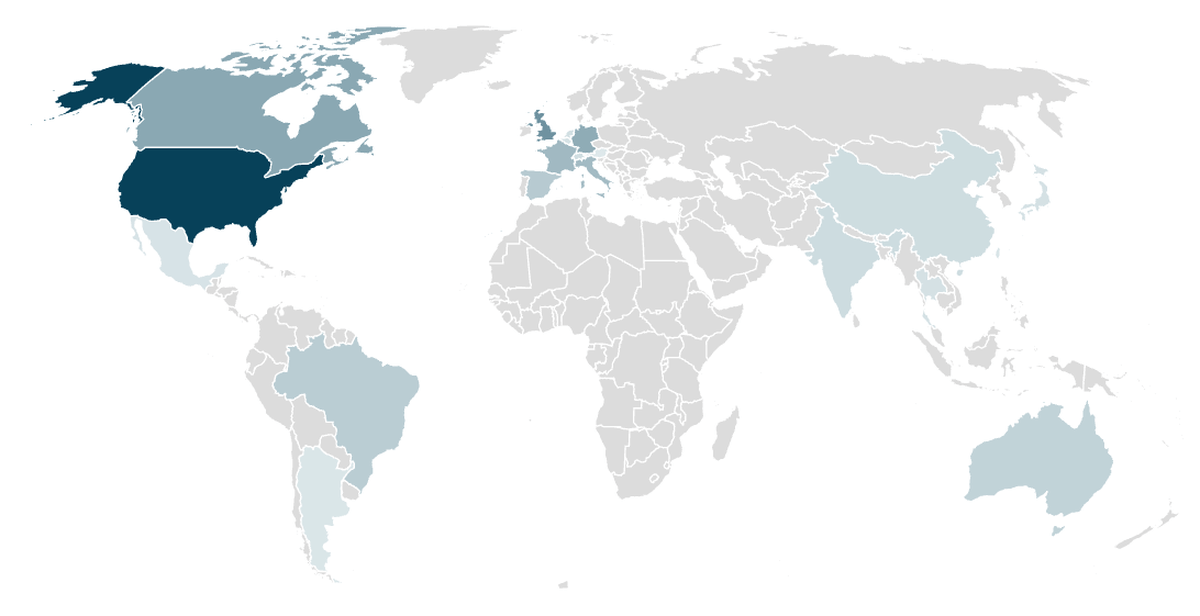
Analyzing the geographical distribution of ransomware victims, the pattern is clearly visible. Western countries suffer the most from economically motivated ransomware attacks. From the 101 different countries that registered victims, 42% of them are from the United States alone, while around 28% come from European countries.
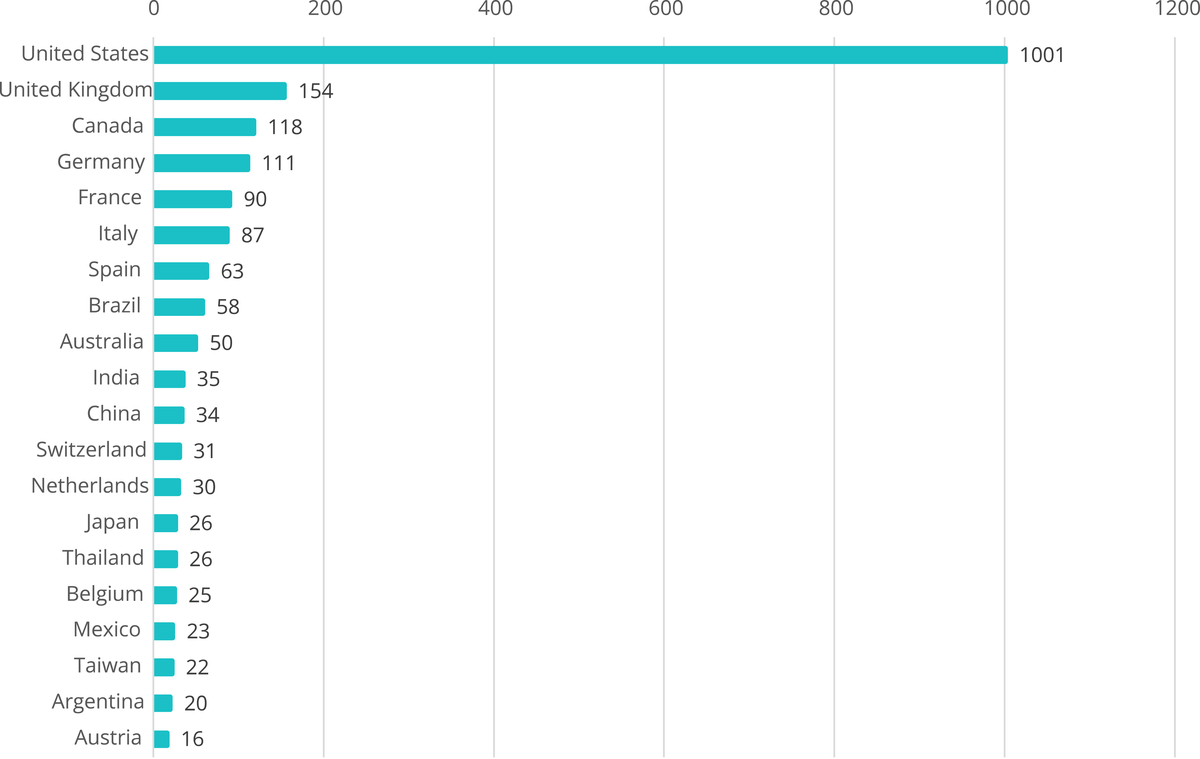
As expected, ransomware victims tend to be based in wealthy western countries, as the RaaS operators tend to make more money out of them.
Conclusion
The RaaS business model has proven to be as destructive for the victims as profitable for the operators involved. Both critical and non-critical companies and institutions are being targeted equally, for the sake of profitability.
Statistics collected this year demonstrate that most RaaS groups do not care about industry sectors if they can extract money from them. The vast majority of Ransomware Groups focus on high-revenue targets, making them a global threat. But this does not mean that companies with a lower level of revenue are exempt from risk. Despite the main targets being high profit companies, small and family-owned companies are also being attacked. In fact, the risk to small businesses has also increased, since overall ransomware activity has been on the rise over the years.
The ransomware group ecosystem has proven to be highly mutable. It is not surprising that a group that is getting a lot of traction suddenly disappears. But the attacks will continue as affiliates will just jump to the next group that they feel works for them.
Our analysts could observe some groups being attacked in August 2022. Although the attribution of these attacks is still unclear, it will be interesting to see how these attacks develop over time, maybe even disrupting their double extortion model for extended periods of time.
Outpost24 advises organizations affected by ransomware to seek guidance from a reliable incident response team and to refrain from paying the ransom.
It is important to note that RaaS attacks start the moment the actors obtain access to the victim’s machine, typically buying it from initial access brokers. Being so, the best way to combat them is before they even have a chance to attack.
Outpost24’s security solutions will help you identify stolen credentials before they can pose a risk to your organization. Moreover, understanding how these groups operate is crucial for strengthening protocols and creating an effective defense against them. Our Threat Intelligence solution provides valuable insights into these groups, including modus operandi, MITRE ATT&CK techniques, IOCs, and much more.
References
CISA. (2022, February 26). Update: Destructive Malware Targeting Organizations in Ukraine. Retrieved January 25, 2023, from https://www.cisa.gov/uscert/ncas/alerts/aa22-057a
CISA. (2020, October 21). Critical Infrastructure Sectors. Retrieved January 24, 2023, from https://www.cisa.gov/critical-infrastructure-sectors
Esparza J.M. (2022, July 8). Ransomware as a Service: Behind the Scenes | Outpost24 blog. Retrieved January 25, 2023, from https://outpost24.com/blog/Ransomware-as-a-service-behind-the-scenes
CISA. (2022, September 6). Alert (AA22-249A) Retrieved January 25, 2023, from https://www.cisa.gov/uscert/ncas/alerts/aa22-249a
Pimenta, B. & López, L. (2021, June 28) Use of Initial Access Brokers by Ransomware Groups Retrieved January 20, 2023, from https://outpost24.com/blog/use-of-initial-access-brokers-by-ransomware-groups/



