Handala Hack Team: Threat Actor Profile
Handala Hack Team, also stylized as Handala_hack, is a hacktivist threat group aligned with pro-Palestinian messaging and Iranian strategic interests. It emerged in December 2023 following the escalation of the Gaza conflict, shortly after the 7 October 2023 Hamas attack on Israel, presenting itself as a pro-Palestinian hacktivist collective. Its operations closely mirror Iranian state-linked activity and indicate a focus on disruption and psychological impact rather than financial gain.
In 2026, Handala Hack Team appears to prioritize targets with symbolic and strategic value, including Israeli civilian infrastructure, Gulf-based energy organizations, and entities linked to Western governments. This targeting reinforces its ideological positioning. Activity increased following Operation Epic Fury in February 2026, indicating responsiveness to geopolitical developments and alignment with broader conflict dynamics.
Multiple intelligence assessments link Handala Hack Team to Iranian state-sponsored activity, specifically the Ministry of Intelligence and Security. Overlaps in targeting, tooling, and messaging have also been observed with clusters such as Void Manticore and Banished Kitten, although this does not constitute confirmed attribution.
The group’s website and Telegram channels have been seized or shut down multiple times, and they now appear to have started promoting Session, a privacy-focused messaging app, as an alternative communication channel by sharing its link with followers.
Following the ceasefire negotiations between Iran and the United States, Handala Hack Team published a message on their official channels claiming the group was acting “according to the orders from the highest leadership of the Resistance Axis.” This type of operational language is notable, as it suggests a level of coordination or strategic alignment that goes beyond typical hacktivist activity. While not definitive, it strengthens the assessment that Handala Hack Team may operate as a proxy or aligned actor within a broader state-linked campaign.
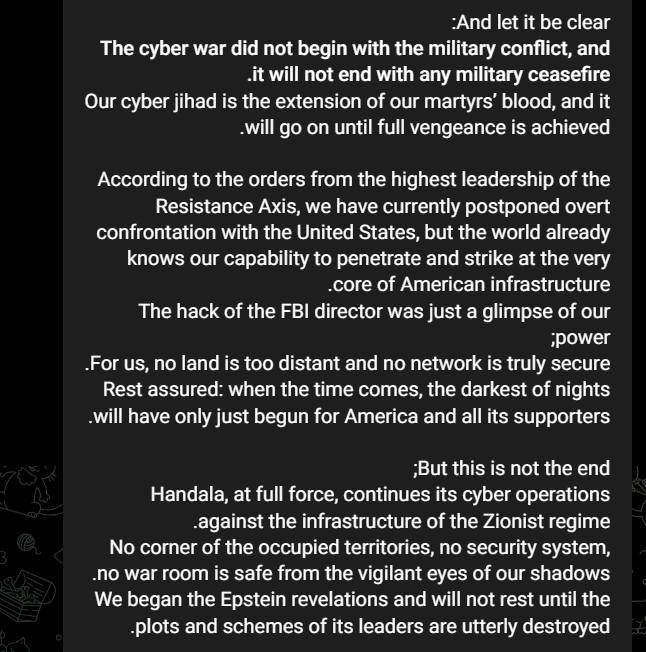
Extract from Handala Hack Team’s message, published following the announcement of a ceasefire between Iran and the United States
Handala Hack Team’s targeting profile and attack techniques
Handala Hack Team consistently targets sectors with high operational and societal impact, particularly healthcare and energy. Additional activity spans financial services, satellite communications, government entities, and military-adjacent organizations. Target selection appears to prioritize both criticality and visibility.
Handala Hack Team’s approach to cyber-attacks combines technical intrusion with coordinated information operations designed to shape perception and amplify impact. Its operations are often paired with public statements, online messaging, and leak claims intended to increase pressure on the victim and extend the psychological impact beyond the initial compromise.
The group’s activity suggests a structured reconnaissance phase focused on identifying viable entry points and supporting infrastructure for targeted attacks, including:
- Gathering victim network information (T1590)
- Gathering victim host information (T1592)
- Identifying IP addresses (T1590.005)
- Acquiring infrastructure and domains (T1583, T1583.001)
The Handala hacking group relies heavily on phishing and credential-based access to gain initial entry into target environments, supported by techniques such as:
- Phishing (T1566)
- Spearphishing links (T1566.002)
- Malicious files (T1204.002)
- Brute force activity (T1110)
- Abuse of valid accounts (T1078) and domain accounts (T1078.002), as well as access through external remote services (T1133)
- Remote Desktop Protocol (T1021.001)
Once inside, the group focuses on credential access, persistence, and lateral movement to expand control within the environment. Observed post-compromise activity includes:
- LSASS memory access (T1003.001)
- Security Account Manager access (T1003.002)
- File and directory discovery (T1083)
- Local storage discovery (T1680)
- PowerShell (T1059.001)
- Windows Command Shell (T1059.003)
- Windows Management Instrumentation (T1047)
- Rundll32 (T1218.011)
- Ingress tool transfer (T1105)
- Scheduled tasks (T1053, T1053.005)
- Network logon scripts (T1037.003)
- Group Policy modification (T1484.001)
The group’s behavior also points to a willingness to cause serious operational disruption, including:
- Disabling or modifying security tools (T1562.001)
- Destroying data (T1485)
- Wiping disk structures (T1561.002)
- Encrypting data for impact (T1486)
Overall, Handala Hack Team combines phishing, credential abuse, remote access, and disruptive or destructive actions with a strong propaganda element, using public claims and leaks to amplify the impact of each operation.
How to defend against cyber threat actors like Handala Hack Team
Handala Hack Team’s operations rely on identifying exposed infrastructure, abusing weak configurations, and using phishing infrastructure to gain initial access. This reconnaissance phase is critical to enabling follow-on intrusion.
To defend against this, organizations need continuous visibility of their external attack surface and early detection of exposures that attackers can exploit. This includes identifying internet-facing assets, misconfigurations, phishing domains, and indicators of external threat activity.
Outpost24’s External Attack Surface Management (EASM) provides continuous visibility into your external assets, helping you identify and reduce exposure before attackers can exploit it. It uncovers unknown, unmanaged, and shadow IT through advanced reconnaissance and AI-driven discovery.
AI-driven risk scoring prioritizes the most critical exposures, enabling teams to focus on what matters most. Continuous monitoring and alerts support early detection and faster remediation. Outpost24’s CompassDRP complements this by providing visibility of cyber threat intelligence into what attackers already know or have access to, including leaked data, compromised credentials, and dark web activity.
Together, EASM and CompassDRP provide visibility into both your external exposure and your external risk.
Strengthen identity security to prevent credential abuse
The Handala hacking group frequently use stolen or compromised credentials to gain and maintain access, leveraging phishing, brute force attempts, and valid accounts.
To reduce this risk, organizations need to prevent weak or exposed credentials from being used successfully. This requires enforcing strong password policies, blocking known compromised passwords, and strengthening identity verification at key access points.
Specops, an Outpost24 company, supports this by strengthening password policy enforcement, preventing the use of breached credentials, and securing authentication and password reset processes. This reduces the likelihood of credential-based access and limits an attacker’s ability to maintain persistence.
Timeline of Handala Hack Team’s recent activity March – April, 2026
April 7, 2026 – Claimed access to Israeli electrical infrastructure and potential military use
The Handala hacking group announced that it had obtained comprehensive access to data pertaining to the sensitive electrical infrastructure of the Israeli government, claiming that this information has been provided to a missile unit currently on standby.
The group reported that all relevant data regarding the critical electrical infrastructure has been extracted and made available to a missile unit in a state of readiness. Additionally, the group asserted that intelligence support for the “Axis of Resistance” is being offered solely by its members, with no involvement from other nations.
April 2, 2026
Handala Hack Team announced the breach of PSK WIND, a command-and-control system related to IDF defense vendors, including air defense and various military installations.
It was not announced that data was wiped, but that confidential information was stolen. It was announced that 14 various organizations, comprising 22TB of wiped data, were attacked.

Handala’s self-published alleged list breached companies
Handala Hack Team’s claim of proof of exploitation
27 March, 2026 – Claimed compromise of FBI Director’s personal email account
Handala Hack Team claimed to have compromised the personal email account of FBI Director Kash Patel, publishing what it alleges to be his résumé alongside a set of personal photographs.
In a statement announcing the hack on its social media channels, the group said: “so-called ‘impenetrable’ systems of the FBI were brought to their knees within hours by our team. This is the security that the US government boasts about?! This is the cyber giant that thinks threats and bribes can silence the voice of resistance?!”
The FBI confirmed that malicious actors had targeted Patel’s email account, assessing that the exposed material is historical in nature and does not contain government information. The agency is offering a reward of up to $10 million for information leading to the identification of individuals associated with the group.
Public reporting indicates that Iranian-linked actors accessed Patel’s private communications in 2024 prior to his appointment as FBI Director. It remains unconfirmed whether this earlier activity is linked to the incident claimed by the group.
26 March, 2026 – Claimed to have breached Lockheed Martin
Handala Hack Team announced via its Telegram channel that it had obtained sensitive information associated with Lockheed Martin. Lockheed Martin is a prominent US-based aerospace and defence company, responsible for the development, production, and ongoing support of a range of military and governmental systems.
Within the same communication, the group published the personal details of 28 Lockheed Martin employees operating in the Middle East. The data released included names, residential addresses, and passport images. The group asserted that these individuals were engaged in “critical” defence projects, specifically referencing maintenance activities for the F-35 and F-22 aircraft. The group also purported to have sent direct messages to the affected employees, warning them to vacate their positions within 48 hours.
In a separate development, a group using the name APT Iran also claimed responsibility for a breach of Lockheed Martin’s systems. This group alleged that it had exfiltrated a substantial volume of data, amounting to 375 terabytes and was demanding a ransom payment of $400 million. According to reports attributed to Flashpoint, APT Iran claimed to possess blueprints for the F-35, the United States’ most advanced fighter jet, as well as additional corporate information.
A spokesperson for Lockheed Martin said the company is aware of the alleged claims.
“We are aware of the reports and have policies and procedures in place to mitigate cyber threats to our business,” the spokesperson told Cybersecurity Dive via email. “We remain confident in the integrity of our robust, multilayered information systems and data security.”
11 March, 2026 – Stryker cyber-attack
Handala Hack Team claimed responsibility for a cyber-attack targeting Stryker, an American healthcare technology company. Public reports indicate that the group asserted it had affected over 200,000 systems and exfiltrated around 50 terabytes of data. Although these claims have not been independently verified, the scale of operational disruption encountered by Stryker positions this event as one of the most notable enterprise cyber-attacks so far this year.
According to Bleeping Computer, which cited an anonymous source familiar with Stryker’s internal response, the attackers may have exploited Microsoft Intune to issue remote wipe commands between approximately 5:00 and 8:00 a.m. UTC on 11 March. This action reportedly impacted up to 80,000 devices enrolled in Stryker’s unified endpoint management service. The use of legitimate administrative tools allowed the disruption to spread rapidly, with employees across multiple regions reporting that their devices had been wiped overnight. Personal devices enrolled in the system were also affected, resulting in the loss of personal data. As the incident unfolded, Stryker instructed employees to power down devices in an effort to limit further damage.
On 15 March, 2026, Stryker stated that it was confident its products and services remained safe for operation and confirmed that no connected products had been compromised. The company emphasised that the incident was not a ransomware attack and that there was no evidence of malware being deployed to its systems. Stryker reported that the situation had been contained and that restoration efforts were progressing steadily.
Let’s talk
If your organization operates in sectors targeted by threat actors, now is the time to assess your exposure. Contact us to speak to an Outpost24 expert, understand where you are most at risk, and what steps you can take to reduce the likelihood and impact of targeted attacks.

