
Is Your LLM at Risk? Explaining Prompt Injection Attacks
Prompt injection attacks are a growing risk in LLMs. Understand how they work and reduce the risk of this LLM-specific vulnerability.
Read moreExpert-led penetration testing across web and mobile apps, APIs, networks, and cloud.
Comprehensive testing and real-time insight to help you uncover, prioritize, and reduce real-world risk faster.

Trusted security testing to identify vulnerabilities and assess the security of your applications, infrastructure, and cloud environments.

In‑depth, expert‑led penetration testing by certified testers to uncover AI and LLM‑specific vulnerabilities across the full AI attack surface.
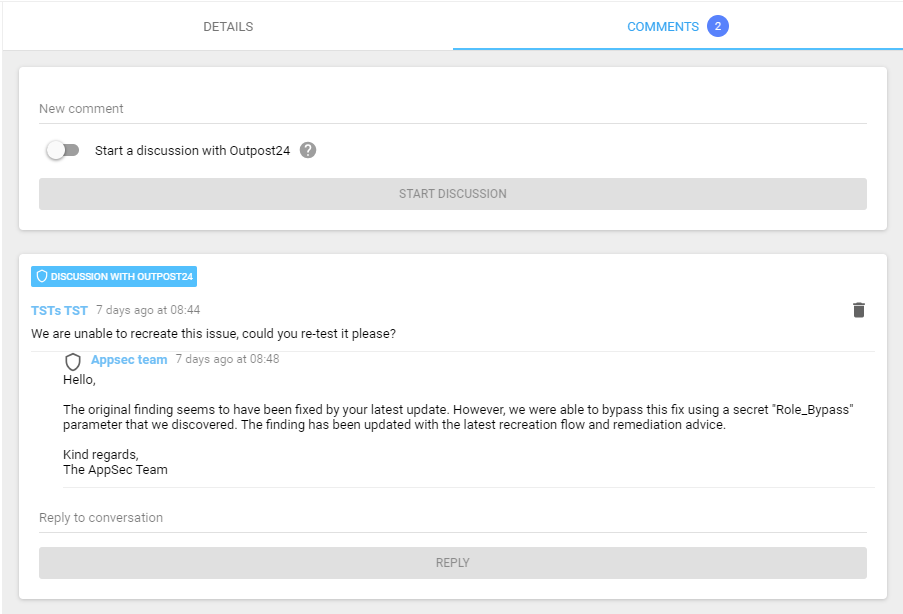
Access penetration tests through a unified platform, view findings in real time, communicate directly with testers, generate reports, and request retesting to verify fixes.
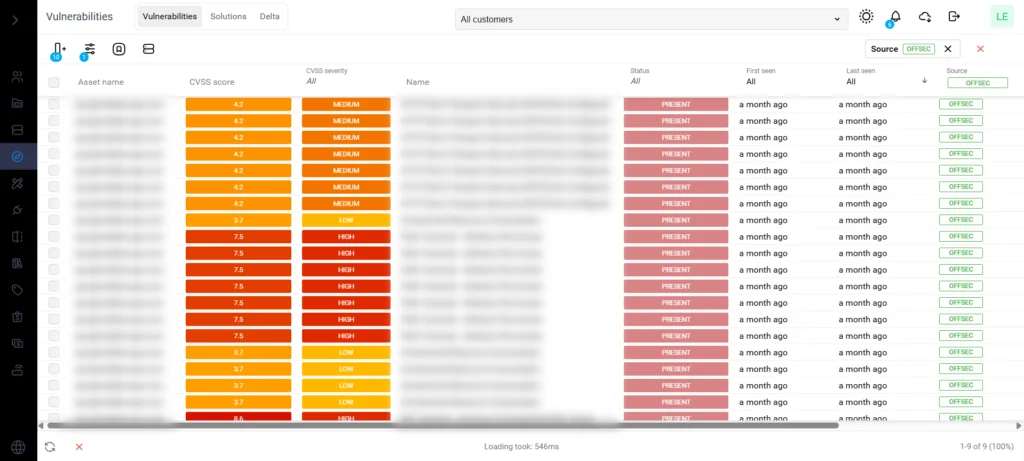
Immediate visibility into findings, with flexible reporting to support remediation and compliance requirements.

Simplify your compliance and audit efforts. Outpost24 Penetration Testing is designed to align with these common regulatory and industry requirements:
A penetration test is an authorized simulated attack on a computer or physical system, performed by penetration testers, to evaluate the security of the system. Penetration testing is often used to complement an organization’s vulnerability management process to ensure security hygiene for better risk management. A penetration test is instructed by an organization on a predefined scope and objective.
Penetration testing is an effective way to detect and remediate flaws in your infrastructure before they turn into a serious threat to your business. It can also be used to report regulatory obligations such as PCI, HIPAA, Sarbanes-Oxley or internal policy compliance like CIS controls.
The length of a penetration test depends on the scope and size of your organization: a network penetration test can take around 2-3 days, applications that require processing vast amounts of data can take up to 10 days, and larger scale physical assessments can take several weeks.
Penetration testing and red teaming serve different purposes, and are dependent on an organization’s security maturity, and testing goals. Penetration testing takes a more general approach by finding and exploiting as many vulnerabilities as possible, in a given timeframe. Red Teaming is a scenario-based attack simulation that will test an organization’s detection and response capabilities against various attacks like ransomware and phishing attempts to provide actionable recommendations for improvements.
CREST is a certification body representing the information security industry. All CREST member companies must undergo a rigorous assessment of their services, processes, and quality to ensure consistency of knowledge against the evolving security backdrop. Outpost24’s SWAT, pen testing as a service for web application security testing, is CREST certified.
Explore additional resources.



Please fill in your information to get in touch with our security experts. All fields are mandatory.
Check our latest research, blogs, and best practices to level-up your cybersecurity program.

Prompt injection attacks are a growing risk in LLMs. Understand how they work and reduce the risk of this LLM-specific vulnerability.
Read more
As AI and LLMs become more integrated with critical business operations, learn why LLM security requires a different approach to traditional cybersecurity.
Read more


AI expands the attack surface. Learn how AI penetration testing helps organizations secure these critical systems.
Read more