How an AI Agent Hacked McKinsey’s AI Platform
Understand how an AI agent hacked McKinsey’s internal AI platform ‘Lilli’, and the lessons organizations should take from this exercise.
Read moreOur Managed Services team act as an extension of your security operations, bringing advanced skills, in-depth knowledge, and expertise to elevate your cyber security program.
Outpost24 Managed Services combine deep in-house product expertise with dedicated security specialists who help you prioritize risks, respond faster, and reduce operational complexity—so your team can focus on what matters most.
Our experts actively manage and optimize your Outpost24 security products, helping you identify, prioritize, and remediate risks faster while reducing the operational burden on your internal teams.

Outpost24 experts continuously monitor your environment using our security products, proactively identifying vulnerabilities, attack surface changes, and emerging threats. Our team validates findings and provides prioritized guidance to help you respond faster and reduce operational burden.

Outpost24 security specialists analyze vulnerabilities and provide clear remediation guidance, helping your team focus on the risks that matter most. This ensures faster risk reduction and more effective use of your internal resources.
Receive structured remediation guidance, executive-ready reporting, and ongoing expert support. This helps your organization resolve vulnerabilities faster, track progress, and maintain clear visibility into your security posture.
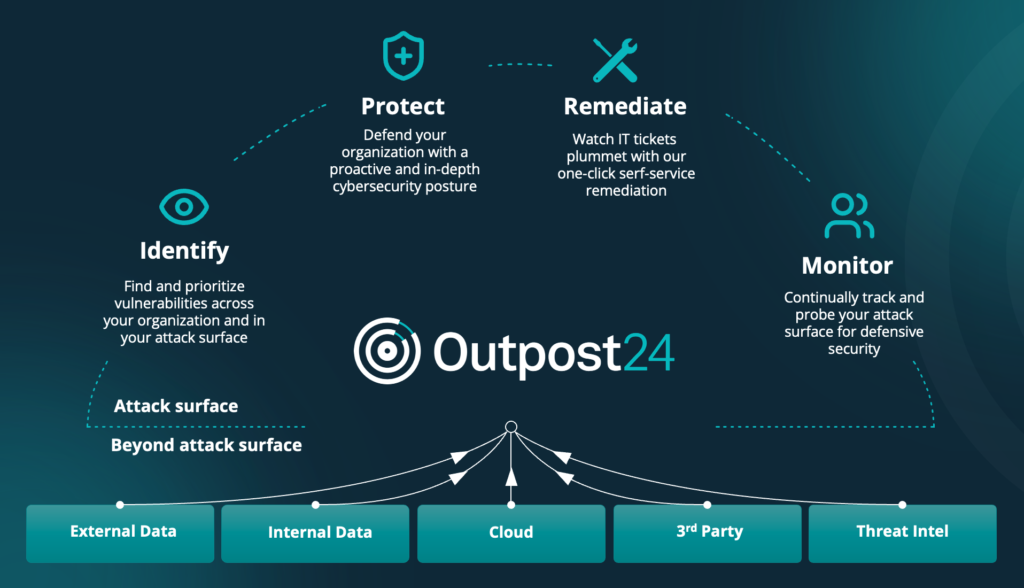
Work directly with the experts behind Outpost24’s security products, ensuring they are configured, optimized, and operated for maximum effectiveness. Their close proximity to the technology enables faster response, more accurate results, and quicker remediation across your attack surface.

Simplify your compliance and audit efforts. Delivered by CREST-certified penetration testers, Outpost24 Managed Services provides trusted security testing aligned with common regulatory and industry requirements:
Explore additional resources.
Please fill in your information to get in touch with our security experts. All fields are mandatory.
Check our latest research, blogs, and best practices to level-up your cybersecurity program.
Understand how an AI agent hacked McKinsey’s internal AI platform ‘Lilli’, and the lessons organizations should take from this exercise.
Read more


Understand the link between evolving cyber threats and the vulnerabilities enabling their success, plus practical advice to close the gaps.
Read more


Today is Microsoft Patch Tuesday for March 2026. There are 83 Microsoft vulnerabilities that have been addressed this time around. The most relevant items…
Read more