
OWASP Top 10 2025: What’s Changed?
See how web application security has evolved and how organizations can stay secure with Outpost24 analysis of the OWASP Top 10 for 2025.
Read moreIdentify, prioritize, and eliminate risks from attackers targeting your organization, across your entire digital attack surface.
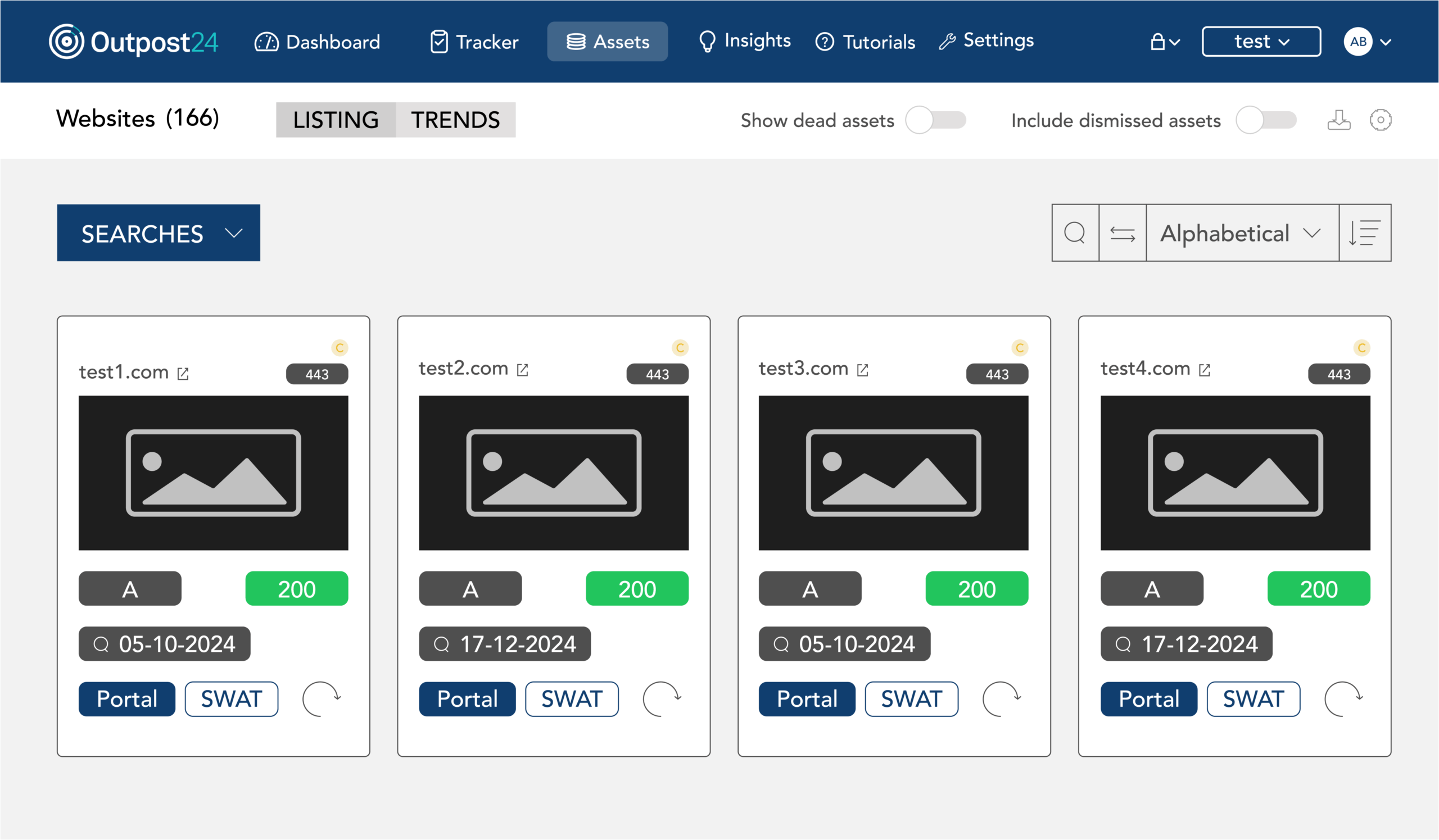
Get a clear, continuously updated view of your external attack surface.
The Outpost24 Exposure Management Platform transforms the way organizations approach cyber security strategy. Moving beyond traditional point solutions, it delivers a flexible, modular framework that provides a comprehensive, continuously updated view of your attack surface, that’s fully aligned to your business objectives.

Continuously track your external attack surface to uncover newly discovered assets, misconfigurations, and evolving threats the moment they appear. Instant alerts and contextual insights enable security teams to act fast and maintain a precise, real-time understanding of their organization’s external risk exposure.

In-depth threat context and insights into attack likelihood and leaked credentials to streamline the prioritization process. This ensures that teams focus on the most critical vulnerabilities first, optimizing remediation workflows.

Powerful, user-friendly technology with actionable insights that deliver results from day one. Providing security teams with clear visibility into the attack surface and assets through flexible packages, so you pay only for what you need.
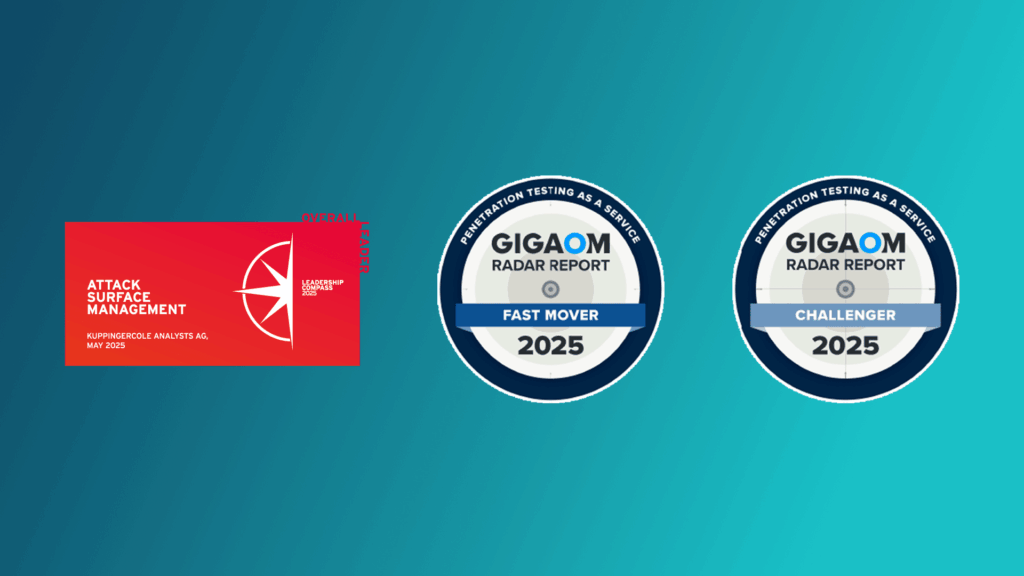
KuppingerCole’s 2025 ASM Leadership Compass:
Outpost24 was the only European Cyber Security Company named an Overall Leader in KuppingerCole’s 2025 ASM Leadership Compass.
We were also recognized as a leader in both the Product and Market categories by KuppingerCole, leading analysts in the areas of digital identities, authentication, and cybersecurity.
2025 GigaOm Radar for Penetration Testing as a Service (PTaaS):
Outpost24 named Challenger and Fast Mover in the 2025 GigaOm Radar for Penetration Testing as a Service (PTaaS)

Simplify your compliance and audit efforts. The Outpost24 Exposure Management Platform is designed to align with these common regulatory and industry requirements:

Expert Help, When You Need It
Extend your team with Outpost24 security experts who continuously monitor your attack surface, investigate exposures, and provide prioritized guidance to help you reduce risk faster.
Explore additional resources.


Please fill in your information to get in touch with our security experts. All fields are mandatory.
Check our latest research, blogs, and best practices to level-up your cybersecurity program.

See how web application security has evolved and how organizations can stay secure with Outpost24 analysis of the OWASP Top 10 for 2025.
Read more


What do you need out of your EASM solution? Read this EASM buyer's guide for 2026 to identify which solution is best for your…
Read more
The OWASP Top 10 for LLM Applications highlights the evolving risks in generative AI systems. Understand the risks and mitigations.
Read more