
Proactive Cybersecurity Strategy: Reducing Risk Ahead of Time
A proactive cybersecurity strategy is no longer optional. Learn why and how you can implement proactive security in your organization.
Read moreComprehensive digital risk insight, focused on what matters.
Monitor leaked credentials, dark web activity, social media impersonation, and exposed data to stay ahead of emerging threats.
Outpost24 Digital Risk Protection delivers a comprehensive, continuously updated view of your external threat landscape, enabling security teams to protect critical assets and stay ahead of adversaries before they strike.
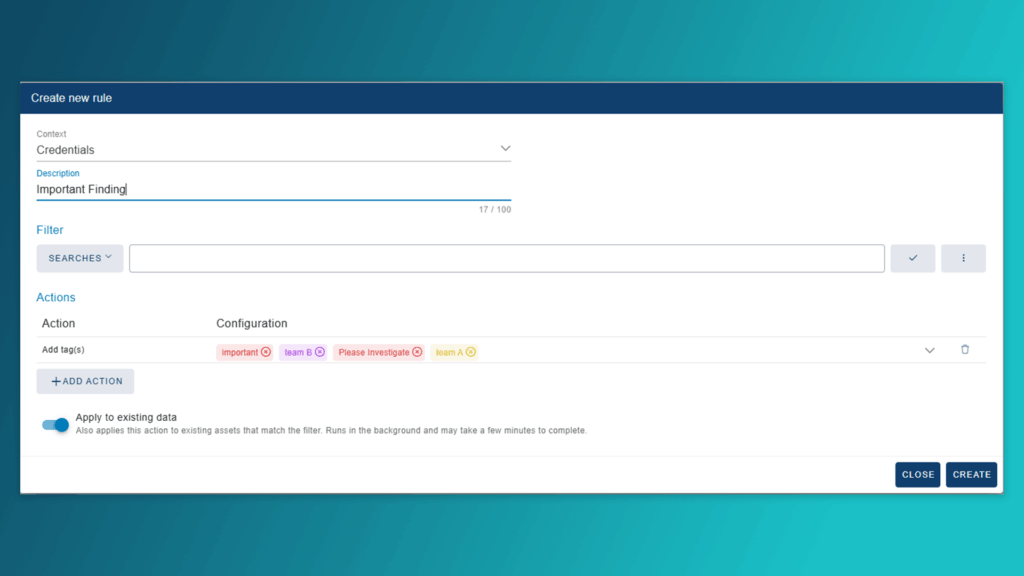
Continuous monitoring, auto-prioritization, and rule-based alerting to reduce manual triage.

Proprietary honeypots, sinkholes, and malware telemetry as well as early visibility into leaked credentials, brand abuse, and underground chatter long before it’s publicly exposed.
Manage all findings from a single dashboard and accelerate remediation through seamless integrations with Jira, ITSM, SOAR, and CAASM.
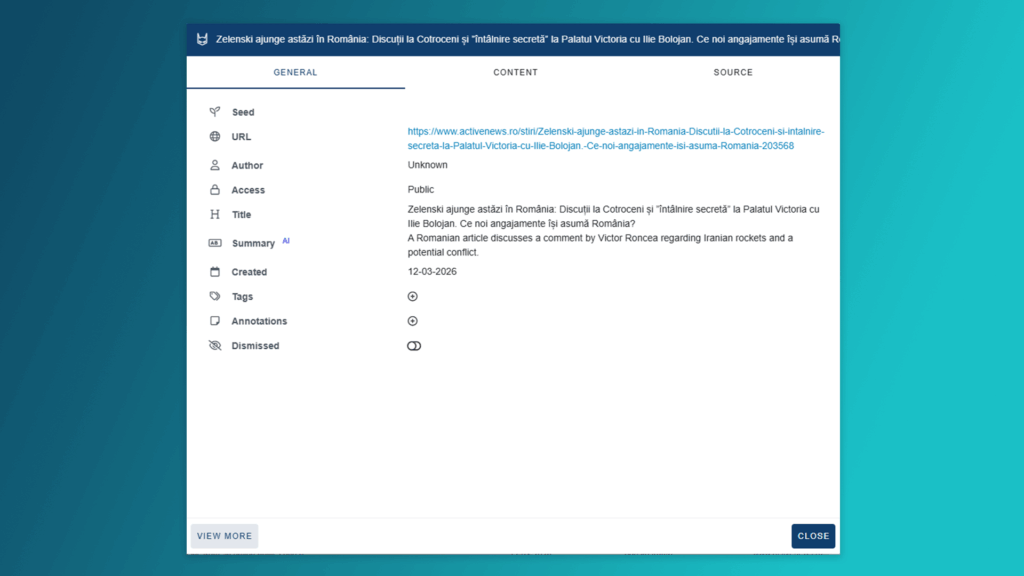
Get AI-enhanced summaries that turn complex, multilingual data into clear insights while preserving the full context for deeper analysis.

Simplify your compliance and audit efforts. Outpost24 Digital Risk Protection is designed to align with these common regulatory and industry requirements:

Our in-house threat intelligence team, KrakenLabs, delivers tailored, in-depth analysis to help you stay ahead of evolving cyber threats. Gain actionable insights into threat actors, IOCs, vulnerabilities, and TTPs targeting your organization along with expert guidance on dark web threats, breach analysis, and OSINT assessments to proactively strengthen your defenses.
Digital Risk Protection refers to the identification, monitoring, and mitigation of digital threats originating outside your network. This includes cyber threats on the open, deep, and dark web, misuse of your brand, leaked credentials, and more.
Our Digital Risk Protection solution, CompassDRP, can detect a range of threats including unauthorized use of assets, phishing sites and malicious domains, leaked or stolen credentials, and data leaks from employees or third parties.
Explore additional resources.
Please fill in your information to submit a demo request. All fields are mandatory.
We’d be happy to schedule a live demonstration of our Digital Risk Protection solution for you.
Check our latest research, blogs, and best practices to level-up your cybersecurity program.

A proactive cybersecurity strategy is no longer optional. Learn why and how you can implement proactive security in your organization.
Read more


2025 has been a summer of high-profile breaches. This post will focus on four notable and high-profile victims: Chanel, Google, Air France, and KLM.…
Read more


In today’s hyperconnected world, a single misleading LinkedIn or X post gone viral can cause problems for the most well established brand in a…
Read more