What to Expect from a Web Application Penetration Test
Web application penetration testing is one of the most important components of an organization’s vulnerability management program. As more critical business processes move online, including customer portals, Software-as-a-Service (SaaS) platforms, APIs and internal tools, web applications have become a primary target for attackers.
According to Verizon’s Data Breach Investigations Report, web applications consistently rank among the most common breach vectors. Attackers don’t need to bypass your perimeter if they can exploit a misconfigured API, an injection flaw, or weak authentication controls in an internet-facing app.
Web application penetration testing helps you uncover these weaknesses before attackers do. It gives security teams a clear view of how an application stands up to real-world techniques and where focused remediation will reduce the most risk.
What is Web Application Penetration Testing?
Web application penetration testing is a process in which methodologies and techniques are used in an attempt to identify security weaknesses and flaws that could allow a malicious attacker to cause harm, or gain unauthorized access to, the resources located in the targeted system (such as credit card information or sensitive personal data). Once the security flaws are identified, analysis of the potential risks and vulnerability impact is provided alongside remediation measures.
According to the Open Web Application Security Project (OWASP):
“A security test is a method of evaluating the security of a computer system or network by methodically validating and verifying the effectiveness of application security controls. (…) Any security issues that are found will be presented to the system owner, together with an assessment of the impact, a proposal for mitigation or a technical solution.”
This concept applies to the web environment; in this case, the targeted system is the web application, and the evaluation is performed in the context of the website and its associated services, rather than the infrastructure in which it is hosted.
How a Web Application Penetration Test is Performed
Web application penetration testing is performed following a given methodology. This is a set of guidelines, rules, and phases that should provide a clear framework which the tester can use to ensure they conduct an accurate and thorough test. There are several different methodologies that testers can follow when performing a penetration test. These include, but are not limited to, the OWASP Testing Guide and Penetration Testing Execution Standard (PTES).
At Outpost24, our tests are performed by experienced and qualified ethical hacking experts, following the Open Source Security Testing Methodology Manual (OSSTMM) by ISECOM when applicable as well as best practices for ISO27005, PCI DSS and NIST standards. Web application security testing is done by using both automated web application assessment tools and manual testing, which ensures all vulnerabilities identified are also manually checked and verified as a result. During the test, our pentesters use web proxies to intercept and analyze the traffic between the web server and the client, amongst other tools.
Phase 1: Discovery and Crawling
Exploring the web application to gather information about the website, its features, and functionality is required to gain a full picture of the web environment. This phase is performed using web application assessment tools, web proxies, and web browsers. The exploration scenarios vary depending on the scope of the assessment.
Phase 2: Vulnerability Assessment
This phase consists of using a wide variety of techniques and tools to simulate several attack scenarios in a controlled way. Here, pentesters attempt to identify and exploit vulnerabilities present in the web application with different approaches. Depending on the scenario, testers can act as a privileged user, normal user, non-registered visitor, or a range of other options.
Simulated attack scenarios can take several forms. For example, a tester may attempt to gain unauthorized access to areas of the application that should only be available to authenticated users or those with specific privilege levels. They may also try to retrieve sensitive information that should be restricted to a defined group of users.
In other cases, the goal may be to manipulate application functionality, such as modifying site content or abusing business logic, to determine whether an attacker could deceive users, escalate privileges, or compromise data integrity.
These testing scenarios include, but are not limited to, the OWASP Top Ten and Web Application Security Consortium’s Threat Classification. Additionally, the status of the web server hosting the targeted application is also checked for possible misconfigurations, which can result in security flaws that could be exploited by an attacker.
Phase 3: Analysis and Reporting
In the final phase, testers analyze the collected data. They gather the necessary evidence of their activities (such as proof-of-concept pieces of code, screenshots and custom developed scripts), and generate a report of the test results. The report provides valuable insight on the vulnerabilities found, explains what the risks are and their impact on the web application and/or the users, alongside a numeric risk score that represents the severity of the vulnerability.
For remediation purposes, the report also includes recommendations on how best to prioritize and fix the vulnerabilities found during the security testing.
Why is Web Application Penetration Testing Important?
The need for web application-oriented penetration testing is mostly driven by the change in the security landscape. With more vulnerabilities being discovered in web-related products and services every year, organizations and vendors are required to keep their knowledge bases and IT infrastructures as up-to-date as possible.
The numbers don’t lie: the total registered vulnerabilities has grown every year since 2016, according to the Common Vulnerabilities and Exposures (CVE) database, skyrocketing from 6,449 registered vulnerabilities in 2016 to 48,488 in 2025:
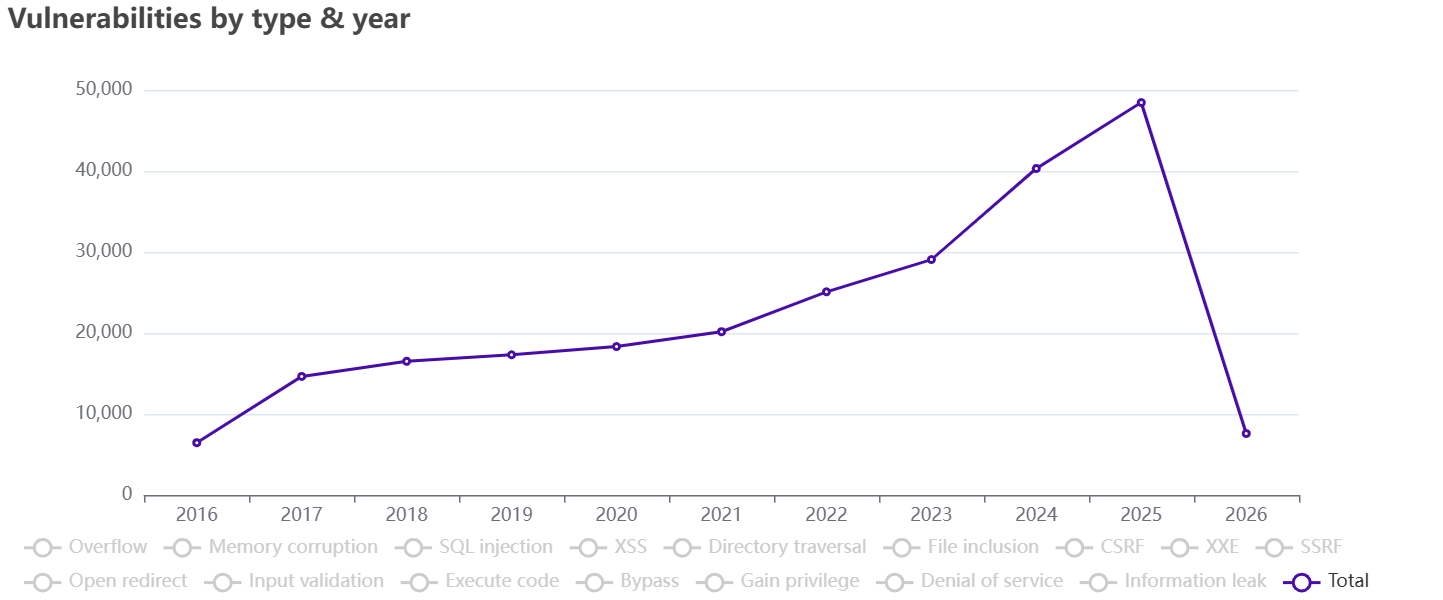
Total number of registered vulnerabilities between 2016 and 2026 (Accurate as of February 2026. Credit: CVEdetails)
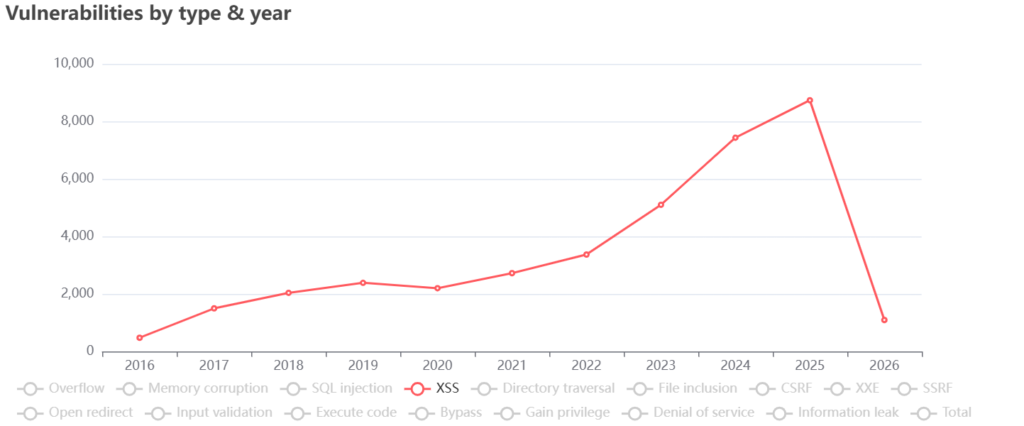
This is truer than ever for web applications. As the development and availability of new technologies such as APIs, IoT devices increased, the amount of potential risks and threats grows. The total amount of published Cross-Site Scripting (XSS) vulnerabilities in the CVE database increased more than tenfold between 2016 and 2025, from 476 in 2016 to 8,736 in 2025 (Figure 2):
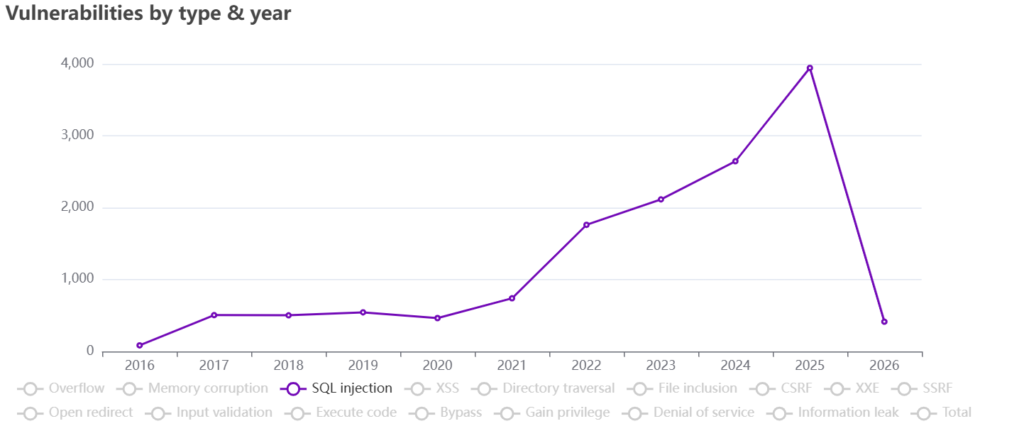
As for SQL Injection (SQLi) vulnerabilities, the increase is stark, growing from just 85 in 2016 to 3,944 in 2025 (Figure 3):
These examples show a growing trend for two of the most critical threats to Web Application Security in the OWASP Top Ten, a widely-known security awareness document with the ranking of the most critical risks for web applications.
Both Cross-Site Scripting and SQL Injection vulnerabilities have been sensationally exploited in malicious attacks. In 2014, Twitter had to shut down their TweetDeck service as attackers discovered a Cross-Site Scripting vulnerability that left millions of user accounts open for a hijack.
Similarly, attackers were able to steal personal data belonging to thousands of World Trade Organization officials around the world through a SQL Injection flaw in the WTO website in 2015.
Security Lifecycle
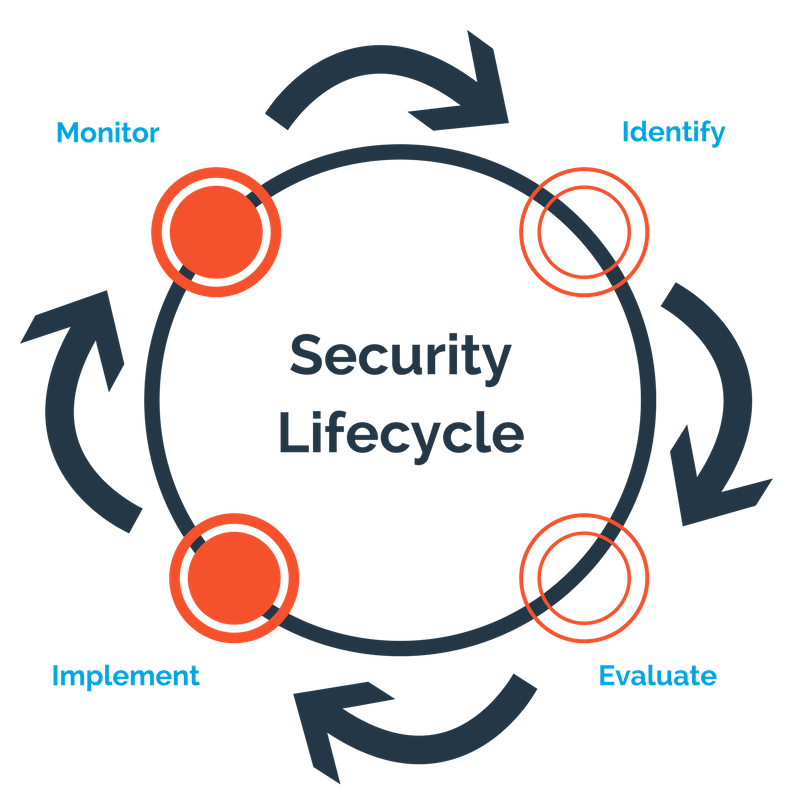
With these in mind, the idea of security can no longer be viewed as static. Instead, organizations need a continuous process that must be maintained over time:
- Identify potential risks and security flaws within the web application’s context
- Evaluate the vulnerabilities existing in the web application by performing a security test
- Implement the security fixes and technical remediation required to mitigate the identified vulnerabilities
- Monitor the effectiveness of the implemented fixes and the security compliance of newly implemented features and components
These phases are executed continuously to identify, evaluate and mitigate vulnerabilities that may affect an organization’s web applications. This allows organizations to maintain continuous control of the security status of the web application and to implement security updates when required. Done well, this heightens the security status of their websites and maximizes the value of performing security tests.
Improving Web Applications Security Status
As vulnerabilities and web-related attacks continues to grow, regular web application penetration testing is essential for organizations to maintain their security status and protect their critical business assets from cybercriminals.
