OWASP Top 10 LLM Risks Explained
The OWASP Top 10 for LLM Applications highlights the evolving risks in generative AI systems. Understand the risks and mitigations.
Read moreComprehensive penetration testing services that continuously uncover vulnerabilities and deliver actionable results through a single platform.

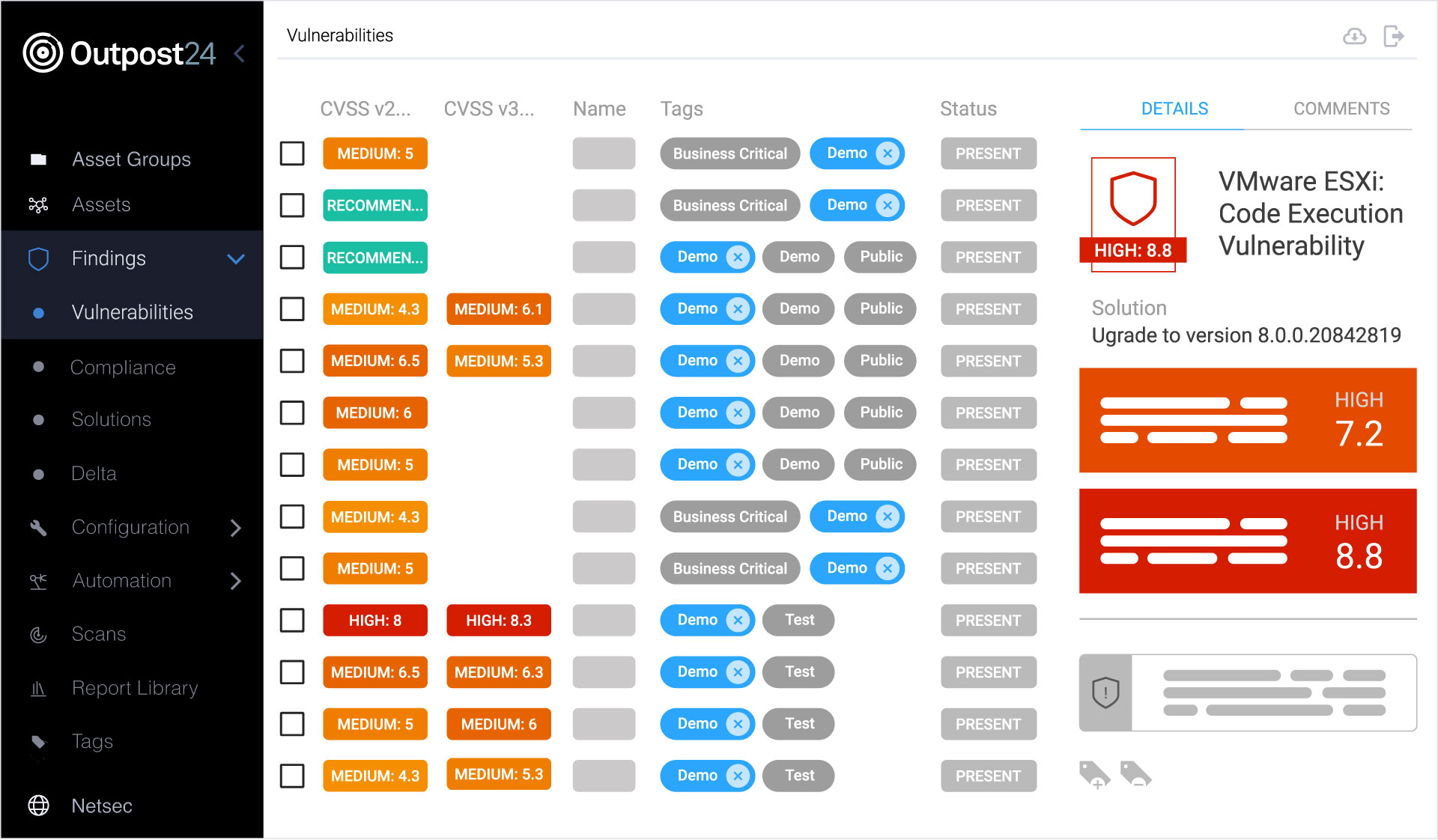
Outpost24 helps organizations of all sizes stay secure and reduce the risk of data breaches through continuous monitoring and expert-verified penetration testing of internet-facing web applications. All results are available in a single platform, with flexible packages tailored to your business.
Certified human expertise and automation for complete coverage.
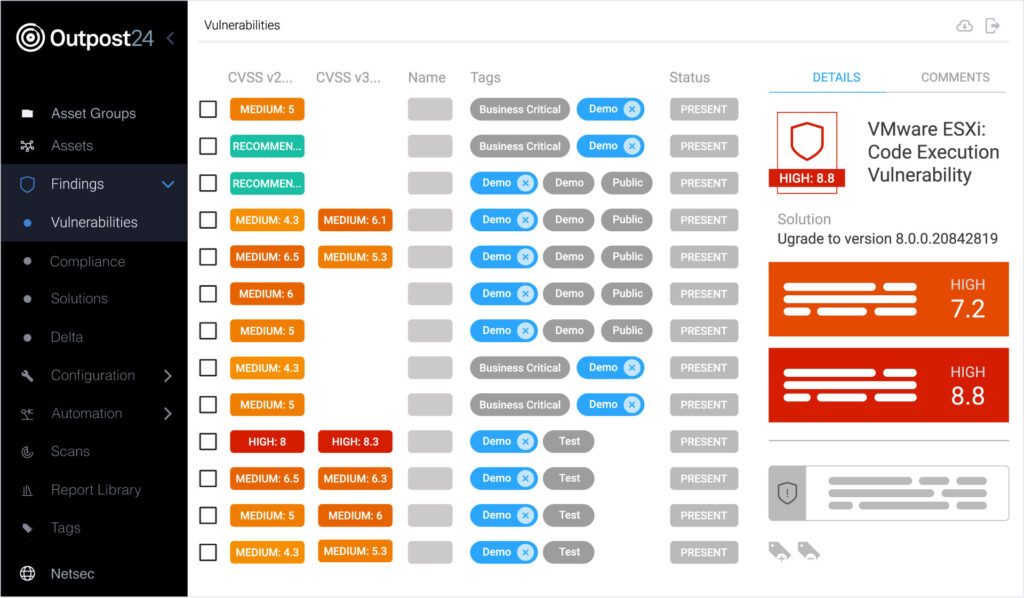
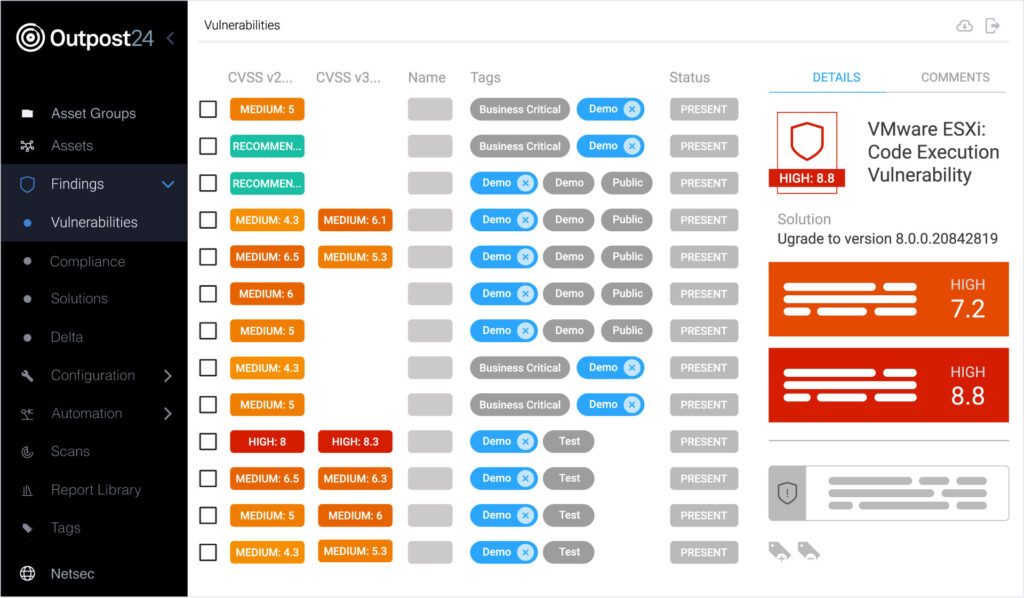
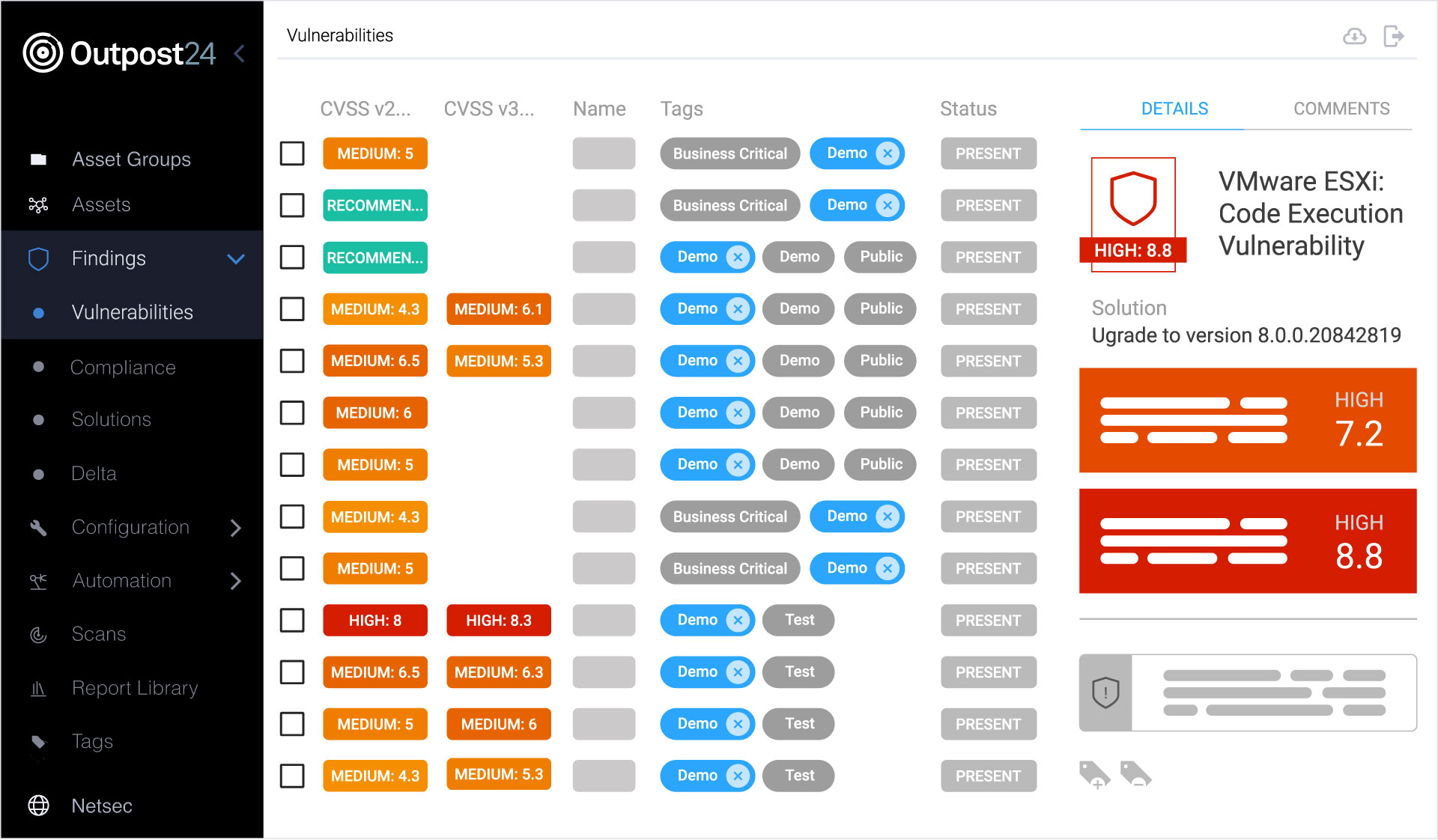
Outpost24 combines human-led penetration testing with automated scanning in a single, unified platform. Certified testers validate findings and focus on real-world application risk, including business logic flaws and unknown vulnerabilities that automated testing alone cannot detect.
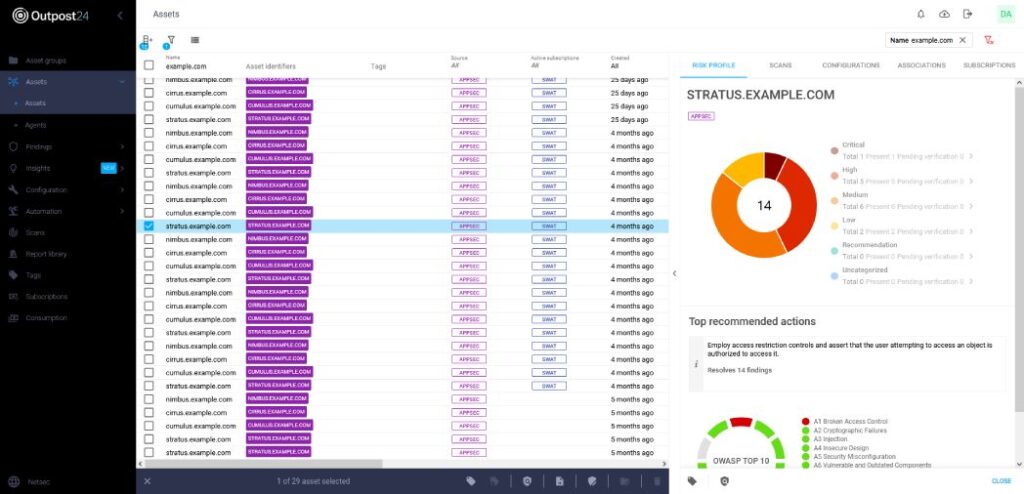
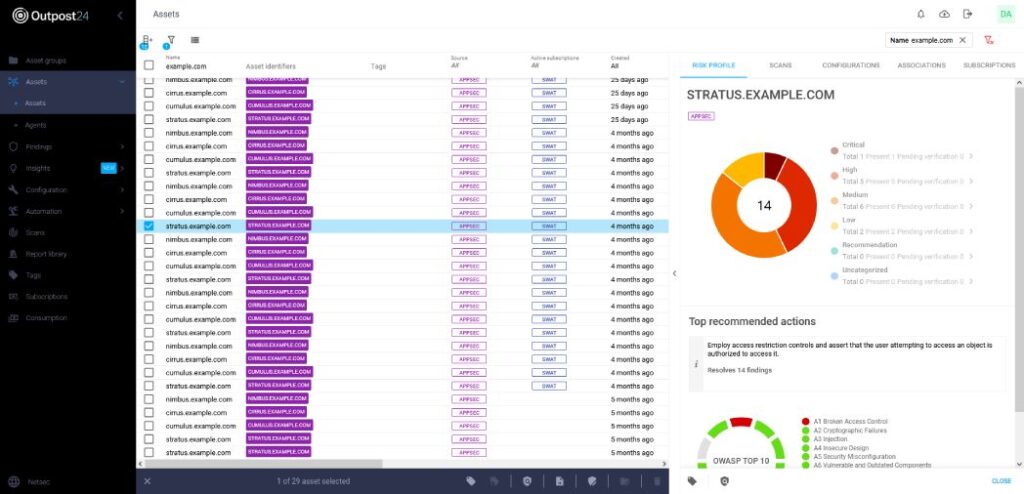
Continuous monitoring with automatic scanning provides ongoing visibility into vulnerabilities affecting your internet-facing applications, helping teams stay informed between penetration testing engagements and respond to newly identified exposure as it emerges.


Built-in REST APIs and webhooks make it easy to connect Outpost24 with existing security and ticketing workflows, including tools such as ServiceNow and Jira, so findings can be managed and tracked as part of day-to-day operations.


The platform enables direct collaboration between developers and certified penetration testers to clarify findings and accelerate remediation. The testing team then verifies fixes to confirm that issues have been properly resolved.


Outpost24 named Challenger and Fast Mover in the 2025 GigaOm Radar for Penetration Testing as a Service (PTaaS).
Our on-demand PTaaS packages include automated and manual penetration testing — all managed within a single platform to streamline testing and reporting.
PTaaS Packages |
SWAT |
Snapshot |
Assure |
|---|---|---|---|
|
Overview
|
A comprehensive PTaaS solution that continuously monitors your business-critical applications with zero false positives and verified results.
|
An in-depth assessment providing a clear view of your application’s security posture to secure new launches and major updates.
|
A baseline assessment of your non-critical applications. Ideal for quick peace-of-mind checks or deeper validation.
|
|
Testing Method
|
Continuous vulnerability scanning and penetration testing (12 months)
|
Manual penetration testing (10 days)
|
Manual penetration testing (3 days)
|
|
Verification of Fixes
|
Ongoing fix verification for 12 months
|
60-day retest window
|
60-day retest window
|
|
AppSec Support
|
Full access for 12 months
|
Access to security tester for 60 days
|
Access to security tester for 60 days
|
|
On-Demand Reports
|
✔
|
✔
|
✔
|


Combine the strengths of Outpost24’s PTaaS with our External Attack Surface Management (EASM) solution to discover, test, and validate both known and unknown applications.


Simplify your compliance and audit efforts. Outpost24 Penetration-Testing-as-a-Service is designed to align with these common regulatory and industry requirements:
PTaaS is a comprehensive security solution that uses automated and continuous testing to identify vulnerabilities in your critical applications, ensuring real-time insights and faster remediation. Our service, fully customizable and backed by EU-based and certified pen testers, provides accurate, in-depth findings verified by our in-house Appsec team and all accessible through a user-friendly portal.
PTaaS differs from traditional penetration testing in that it offers continuous, automated security assessments and real-time insights, whereas traditional penetration testing is typically a one-time or periodic manual process. PTaaS also provides ongoing support and customizable solutions, ensuring that your security measures stay up to date with the latest threats.
Outpost24’s PTaaS offers extensive and custom manual testing, with the option to automate scans for continuous monitoring. Unlike traditional pen testing delivery, Outpost24’s findings are delivered in real-time via a dedicated portal that also connects you directly with our security experts.
PTaaS allows agile organizations to expedite remediation during testing, and includes continuous monitoring to minimize your application attack surface. Outpost24’s approach to PTaaS also guarantees zero false positives, as findings are produced and verified by security experts.
Yes, Outpost24 will verify the effectiveness of your remediation beyond the test length.
Our risk-based approach helps you prioritize remediation efforts based on the highest risks posed to your business.
Yes, the reports can be exported to PDF, Excel, and XML. The report data is fully configurable and can be presented in both technical and business context, depending on the audience.
PTaaS eliminates the need for frequent vendor rotation by streamlining the pen testing process. Traditional pen testing often involves onboarding new vendors, which can be both time-consuming and costly. Some organizations choose to rotate vendors in order to benefit from different testers’ specializations and expertise, as each tester may uncover vulnerabilities that others might miss. However, with PTaaS, this concern is effectively addressed. Outpost24’s PTaaS offers a larger pool of skilled testers and encourages creative testing, ensuring a fresh perspective on your web application security. Our experts are always on standby to address any problems that arise, providing comprehensive coverage and eliminating the hassle associated with vendor rotation.
Explore additional resources.


Please fill in your information to submit a demo request. All fields are mandatory.
Check our latest research, blogs, and best practices to level-up your cybersecurity program.
The OWASP Top 10 for LLM Applications highlights the evolving risks in generative AI systems. Understand the risks and mitigations.
Read more


As application vulnerabilities build and threaten security, learn how combining EASM and pentesting can proactively secure your organization.
Read more


Prompt injection attacks are a growing risk in LLMs. Understand how they work and reduce the risk of this LLM-specific vulnerability.
Read more