
Stryker Hack: What We Know So Far
Understand what happened in the recent Stryker hack with expert analysis from the Outpost24 Threat Intelligence team.
Read moreMachine Readable Threat Intelligance (MRTI) feed to power proactive cyber defense.
Continuously enrich your defenses with real‑time Machine Readable Threat Intelligence (MRTI) that’s easy to deploy, fully integrated, and focused on protecting your assets from online attacks.
Actionable threat intelligence feed for faster, clearer results and more effective prioritization.
Access to open, private and propriety sources, delivered using STIX / TAXII 2.1 industry standards for enhanced information sharing and collaboration.
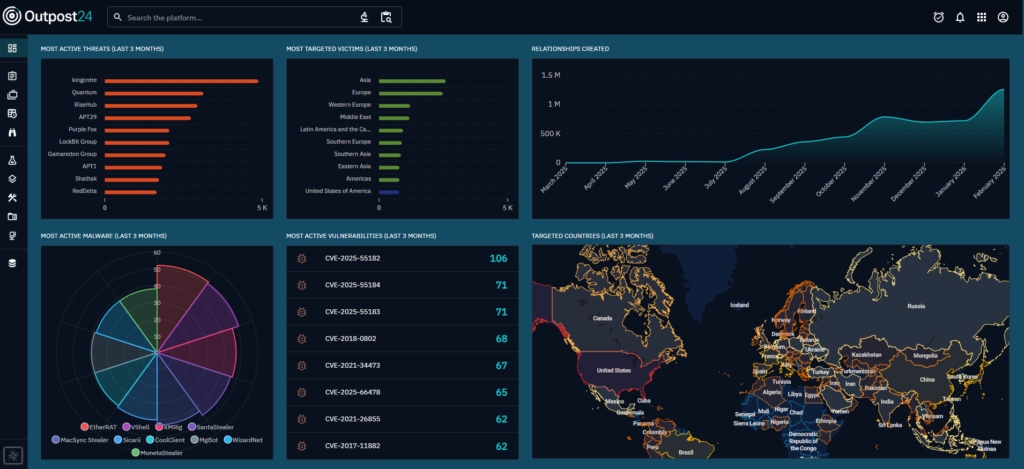
Image shows an example of the MRTI feed integrated into OpenCTI.
Enriched and technical indicators help security teams define tactical blocking rules and make informed strategic decisions.
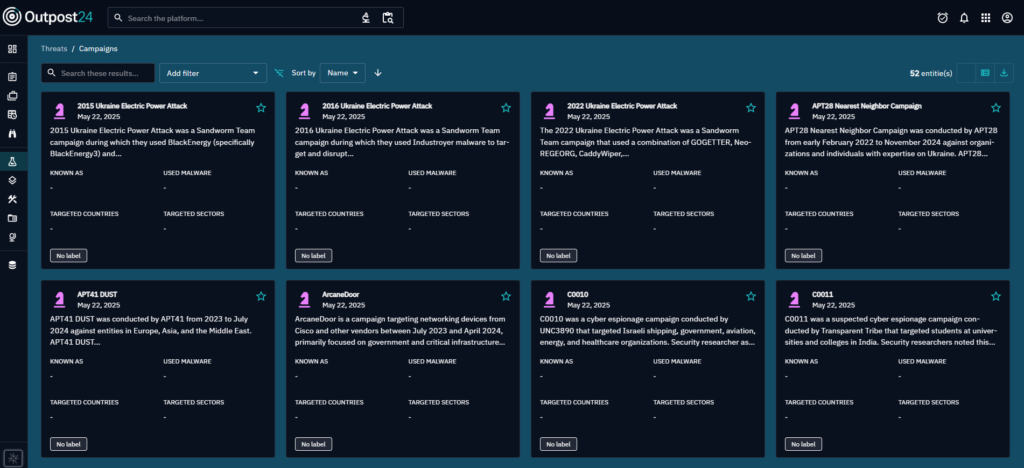
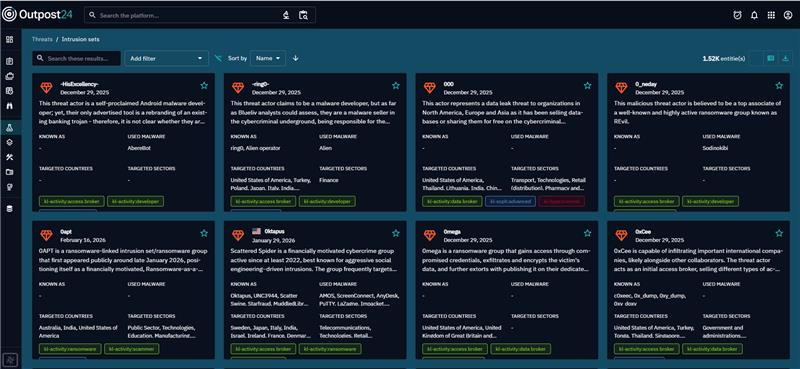
Strategic threat intelligence focused on threat actors, context, and behaviors providing security teams deeper visibility and insights into who is behind malicious activity.

Simplify your compliance and audit efforts. Outpost24 MRTI Feed is designed to align with these common regulatory and industry requirements:

Our in-house threat intelligence team, KrakenLabs, delivers tailored, in-depth analysis to help you stay ahead of evolving cyber threats. Gain actionable insights into threat actors, IOCs, vulnerabilities, and TTPs targeting your organization along with expert guidance on dark web threats, breach analysis, and OSINT assessments to proactively strengthen your defenses.
Outpost24’s MRTI Feed is a machine‑readable threat intelligence stream, delivering ultra‑fresh indicators of compromise (IOCs) such as crime servers, malware, attacking IPs, as well as strategic information like Threat Actor information, TTPs, and their relationships to the IoCs. By ingesting this data into your existing security tools, your team can identify threats faster, reduce blind spots across the open, deep, and dark web, and respond to attacks before they impact critical assets.
Outpost24’s MRTI Feed combines data from a wide range of open, private, and proprietary sources, including malware analysis, honeypots, spam mailboxes, sinkholes, and our in-house Threat Intelligence team research. This multi‑sourced approach provides broad coverage of attacker infrastructure and behavior, minimizing gaps in your external threat visibility.
All data is translated into machine‑readable formats for rapid consumption by your security stack. MRTI Feed supports STIX/TAXII 2.1, which can be directly integrated in most SIEMs and other security products such as Splunk, Sentinel, and QRadar. This allows you to enrich alerts, create dynamic blocking rules, and automate responses without re‑architecting your environment.
MRTI Feed is simple to set up and can be integrated into your SIEM, firewalls, IPS, and other security controls in a matter of minutes. Because the feed is continuously updated in real time, customers typically start seeing high‑impact results for more efficient threat triage across their environments.
Explore additional resources.


Please fill in your information to get in touch with our security experts. All fields are mandatory.
Check our latest research, blogs, and best practices to level-up your cybersecurity program.

Understand what happened in the recent Stryker hack with expert analysis from the Outpost24 Threat Intelligence team.
Read more


The Outpost24 Threat Intelligence team research Handala Hack Team, the group claiming responsibility for several high-profile cyber-attacks.
Read more
Understand how an AI agent hacked McKinsey’s internal AI platform ‘Lilli’, and the lessons organizations should take from this exercise.
Read more