The seven most common web application attack vectors
Modern web applications are complex, it is often made up of many layers where potential flaws could appear making it hard to secure. That’s why it’s important to understand the key attack vectors hackers use to spot entry points and map your attack surface during reconnaissance and work back from there to protect your web application footprint.
Web application attacks are the new norms
Web applications are often the shop window to your business for a hacker and is where both client and financial information is held. With a global lockdown creating upheaval for enterprises globally and with increased web attack surfaces to contend with, hackers continue to relent by changing up their tactics to create more havoc and spread attacks for malicious gain. Hackers use dangerous mechanisms to find opportunities to break into organizations’ web apps to steal vital information and impact the businesses who own them. Successful web application attacks pose a serious threat to businesses, they account for almost half of all data breaches (43%) in 2019 and is the single greatest cause of data breach according to the Verizon DBIR 2020 report.
Even with a good level of security hygiene, such as running software updates, patching and encryption, hackers are getting increasingly sophisticated and skilled at finding hidden vulnerabilities without you knowing. In 2019, even the biggest brands fell short in protecting their applications with incidents ranging from lack of authentication controls (First American Financial), publicly available servers (Facebook) and the infamous Fortnite breach when a vulnerability allowed a cross-site scripting (XSS) attack where thousands of users were tricked into clicking a link planted by a hacker, contributing to millions, even billions, of customer data being leaked.
The art and science of reconnaissance
Reconnaissance is an important process for hacking as it is the first step in the infamous cyber kill chain. It’s hacking 101, and often referred to as ‘footprinting’ where information is gathered to identify weaknesses and when opportunities are validated, and an attack plan is built upon. It’s the preparatory phase, where hackers will collect as much information as possible about the target before striking at the right time.
Different techniques are used during this phase and involve ‘direct’ or ‘passive’ approaches depending on whether information is collected with/ without accessing the target. From a security perspective you want to ensure your organization’s web apps are secured on all sides, all year around so no adversary on a reconnaissance mission spots anything they can get their teeth into.
The stakes are extremely high for businesses who underestimate the complexities in web apps and the techniques used by hackers. The slightest error spotted could give them a foothold to your crown jewels and get a piece of your pie without you noticing.
Mapping your overall web application attack surface
1. Application discovery
The first challenge is application discovery – understand what critical web apps you own and where they are exposed, which can be impossible as these can run into the 100s/1000s due to shadow IT in large organizations. Hence we recommend taking a strategic view by focusing on the business critical web apps and assessing their risk level first.
2. The 7 deadly vectors for web application vulnerabilities
To help you better understand the different mechanisms hackers could use during reconnaissance we have broken this down into the 7 common attack vectors that lead to software vulnerabilities, which determines the complexity of your application:
- V1 Security mechanisms (SM): How the traffic between users and the application is secured i.e is there authentication in place?
- V2 Page creation method (PCM): This depends on the code the website has been developed in i.e some code languages are more exposed than others and as new versions are released this will fix these issues. Developing a website with insecure code means there are allot more potential vulnerabilities from old and not up to date code which is easy for a hacker to exploit.
- V3 Degree of distribution (DOD): The more pages you have, the more risks there are, therefore all pages must be identified and vulnerabilities uncovered at all levels.
- V4 Authentication (AUTH): Authentication is the process of verifying the identity of an individual accessing your application. Access to certain actions or pages can be restricted using user levels set up by the administrator and critical to keeping the bad guys out.
- V5 Input vectors (IV): The attack surface increases with the number of different input fields you have on a web application and can lead to XSS attack.
- V6 Active contents (ACT): As soon as an application runs scripts, we have active contents and depending on the way those scripts have been implemented, the attack surface could increase if a website has been developed using several active content technologies.
- V7 Cookies (CS): Cookies are essential for real time application security, by monitoring session activity and ensuring anyone who sends requests to your website are allowed access and keep hackers away from unauthorized areas.
3. Temporal and environmental risks
After discovering your web apps in the public domain and scanning them against the 7 common attack vectors and calculating your applications complexity level. We correlate the results against the temporal and environmental factors that could impact the risk posture:
- Business criticality: Is your web application business critical and will you lose revenue if it goes down? Or, does the application hold customer data (PII) sitting behind a username and password? Establishing this helps us understand the business criticality level of the application.
- Update frequency: Not all applications are updated regularly and stay static with little intervention whereas some applications with dynamic content and have many functionalities that makes it more vulnerable for attacks
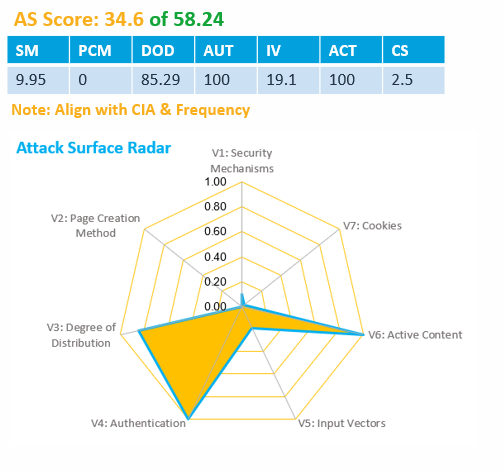
The final result provides you with a blueprint of your attack surface, where a radar of your weaknesses and overall risk score is clearly defined and highlighted. You can then take the decision to shut down (if the app is no longer used and left online) or to focus vulnerability assessment and remediation efforts on the areas that poses the highest risk for your organizations.
Put your (security) money where your mouth is
This approach ensures you can make the best decisions on how to assemble the optimal application security testing program and where to spend your budget wisely.
The scoring matrix and attack surface radar map for your application will visually identify where the surface is and based on the 7 deadly web attack vectors . This map will help to show the different weightings of how the score has been calculated and you can truly understand where a hacker will be able to find more pathways and hence add more security defences.
This level of detail allows application security managers or teams to create a continuous assessment program by narrowing down what they own, pinpointing the biggest risks and protecting critical apps that grow and support your business, rather than wasting time and resources on apps you no longer need. For more matured organizations, feeding this information back in a continuous cycle as more apps are added to your digital footprint so you always stay ahead of hackers as the market changes.
Get started with application attack surface discovery and management
Tried and tested by our enterprise customers, these metrics have been built by our security experts to enable better decision-making. Utilising a detailed assessment tool and framework like Outpost24 to truly understand your attack surface and a risk score will help you to easily identify those applications that pose a direct threat from hackers from the start.
If you are in doubt about your application security posture get in touch now to score and build a tailored and relevant security program for your business.
